Requirement:This article explains on how to configure the management login against AD using MSCHAPv2 with Clearpass as RADIUS server.
When we configure a TACACS authentication service in CPPM to authenticate Aruba OS Management users, it uses PAP as the authentication method by default.
Solution:If we want to use MSCHAPv2, we need to create Radius Enforcement Generic Service in CPPM and configure CPPM as Radius Server in the controller.
Configuration:1. Login to ClearPass Policy Manager and navigate to Configuration --> Services. Click on Add a Service and select the type as RADIUS Enforcement (Generic). Specify a name and service rules using the any of the Radius Input attributes. (Eg: We can make use of Radius:IETF attribute that will be equal to 6 for an administrative-user login requests). Click Next.
2. Select the authentication method as MSCHAP. If you have already created Active directory authentication source, select it from the drop down for authentication sources. If not, use 'Add new authentication source' hyperlink and create a new Active Directory authentication source. Make sure to include the newly created Active Directory authentication source in the service.
3. Create an Enforcement profile: Navigate to Configuration --> Enforcement --> Profiles --> Click on Add. Select the template as Aruba Radius Enforcement. Specify a name and click on attributes tab and specify the name of the user-role that will be sent across if a specific enforcement condition matches. Note that this user role needs to exist in the Aruba Controller for Management users. By default, Aruba controller has root, read-only, guest-provisioning, local-api-mgmt & network-operations for management users.

4. Create an Enforcement policy: Navigate to Configuration --> Enforcement --> Policy --> Click on Add. Create a Radius Based enforcement type with default profile set to deny access profile so that clearpass sends access-reject, if none of the enforcement conditions are satisfied. Navigate to rules and specify the enforcement conditions to required enforcement profile.

5. Map the Enforcement Policy to the Service. Role Mapping may or may not be configured based on the requirement. If role mapping is required, enforcement policy conditions should be created accordingly.
6. Service Configuration Summary Screenshot:


7. ClearPass Server should be joined to the Active directory domain for MSCHAP/MSCHAPv2 authentication. We can check the same by navigating to Administration ---> Server Manager ---> Server Configuration ---> Click on the respective server and it will show you the list of the Active directory domains that CPPM is a part of.
8. Controller configuration screenshot:

VerificationAccess tracker Screenshot for Verification:
1. Access tracker Summary:

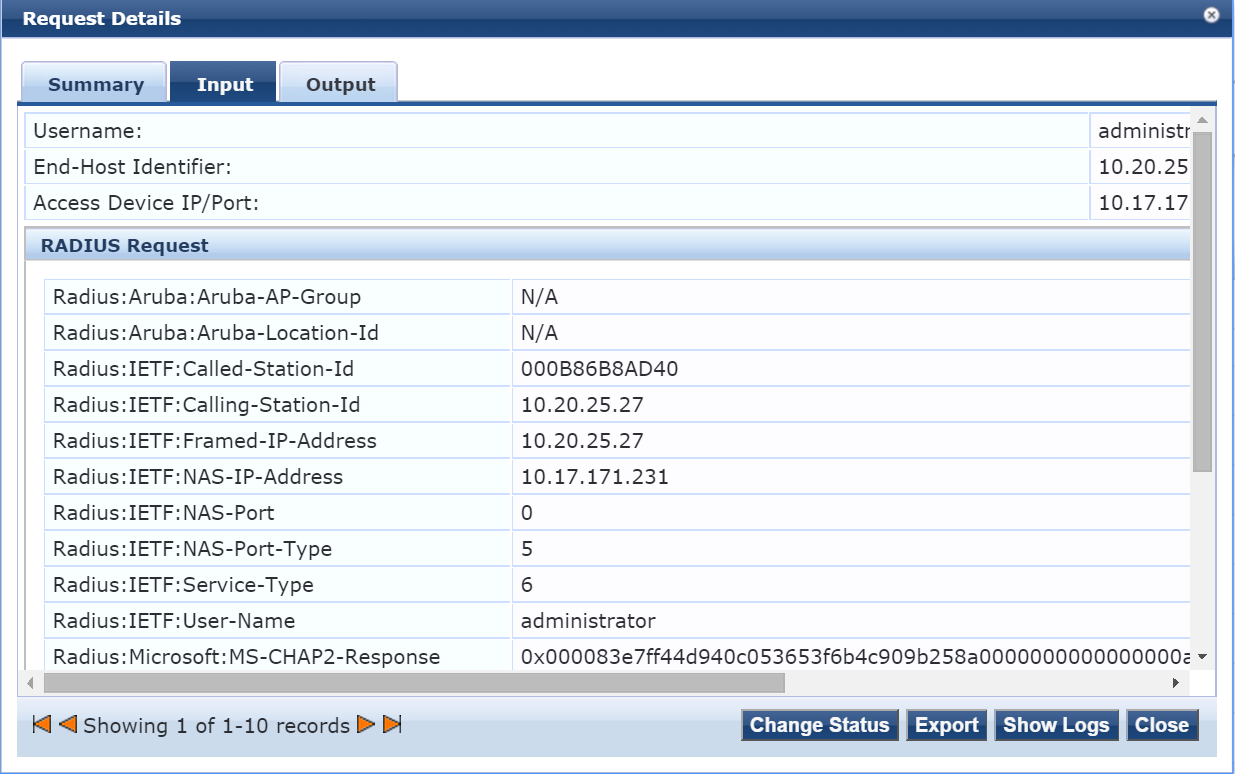
2. Access tracker Input Radius attributes:
Access tracker Output:
