PBR is used to route packets based on a certain policy. Unlike traditional destination IP based routing, ACLs are used to determine the routing path. ACL characterizes the packet on its source/destination IP address, L4 protocol and ports, and also the kind of application (appRF).
Feature introduced from AOS 6.4.3
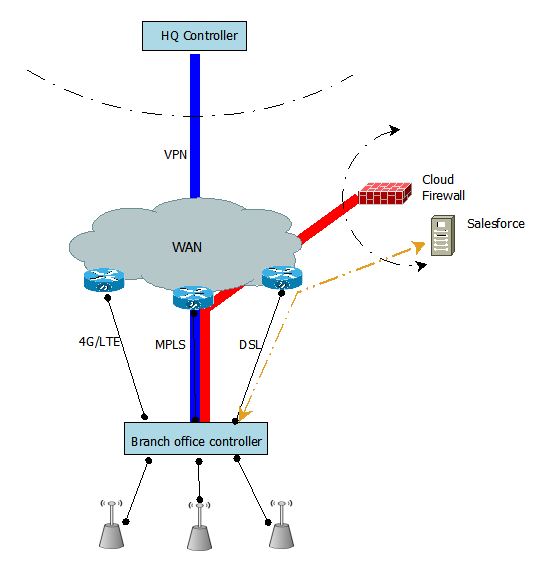
Network Topology
Need to have PEF license for creating ACL.
(6.4.3-Beta-Master) (config) #show license
License Table
-------------
Key Installed Expires Flags Service Type
--- --------- ------- ----- ------------
VJJpNB4W-Vy661uqG-zYDDAqx+-AcDqHo7W-y5i67c7K-UTk 2014-11-27 Never E Next Generation Policy Enforcement Firewall Module: 128
21:55:24
ro8x99xG-ZB5XWMqH-XdCHG0sp-SkV6MZTs-wugFRyfu-pyk 2014-11-27 Never E Access Points: 32
21:55:34
e07GEm/S-cZeLd/1F-DY+NKjxf-UTD/nfCR-4teUYtTW-KO4 2014-11-27 Never E Policy Enforcement Firewall for VPN users
21:55:44
1vVO6Tf1-RXyAXDMh-loBSuTA7-4vxeVnk3-hSMoFey2-fBE 2014-11-27 Never E RF Protect: 32
21:55:55
License Entries: 4
Flags: A - auto-generated; E - enabled; R - reboot required to activate
(6.4.3-Beta-Master) (config) #
1) Create a Next hop list
2) Create a route ACL with PBR option required
3) Bind the ACL to user role or VLAN interface
To create a PBR based ACL:
1) Create a Next hop list
(6.4.3-Beta-Master) (config) #show ip nexthop-list
Nexthop-List Entries
--------------------
Nexthop-list Name Nexthop-list Id Preemptive Failover Active IP Nexthop IPs(Priority)
----------------- --------------- ------------------- --------- ---------------------
Branch-with-multiple-uplinks Enabled 10.17.170.40(40), 10.17.168.200(30), 10.17.169.200(20), 10.17.164.254(10)
test Enabled 10.17.168.193(128), 10.17.169.200(128), 10.17.164.254(128)
2) Create a route ACL with PBR option required
(6.4.3-Beta-Master) (config-route-test)#network 10.0.0.0 255.255.0.0 any any route ?
ipsec-map Forward packets to ipsec tunnel
next-hop-list Forward packets to nexthop list
tunnel Forward packets to L3 tunnel
tunnel-group Forward packets to tunnel group
(6.4.3-Beta-Master) (config-route-test)#network 10.0.0.0 255.255.0.0 any any route next-hop-list test
(6.4.3-Beta-Master) (config-route-test)#exit
(6.4.3-Beta-Master) #show ip access-list test
ip access-list route test
test
----
Priority Source Destination Service Application Action NextHopList IpsecMap Tunnel TunnelGroup IPv4/6
-------- ------ ----------- ------- ----------- ------ ----------- -------- ------ ----------- ------
1 10.0.0.0 255.255.0.0 any any forward test 4
(6.4.3-Beta-Master) #
Use the following commands to understand the behaviour:
(6.4.3-Beta-Master) #show datapath route-cache
Route Cache Entries
-------------------
Flags: L - Local, P - Permanent, T - Tunnel, I - IPsec,
t - trusted, A - ARP, D - Drop, R - Routed across vlan
O - Temporary, N - INactive, H - DHCP snooped
IP MAC VLAN Flags
--------------- ----------------- ----------- ------
172.16.0.254 00:1A:1E:01:2D:18 1 LP
10.17.168.200 00:1A:1E:01:2D:18 174 LP
10.17.170.40 00:1A:1E:01:2D:18 187 LP
10.17.169.200 00:1A:1E:01:2D:18 183 LP
10.17.164.230 00:1A:1E:01:2D:18 164 LP
10.17.164.254 00:1A:1E:09:15:C0 164 tA