Q: What is Auth survivability ? What are the auth methods supported ? How Auth survivability works ? How to configure and verify ?
A: What is Survivability :
- Allows Aruba controller to provide authentication and authorization survivability when remote authentication servers are not accessible.
- Stores user access credential as well as Key reply attributes with external authentication server.
- Maintains the connectivity for authenticated users.
Auth methods Spported :
Captive Portal Clients: PAP method.
802.1X clients
Termination disabled:
EAP-TLS with external RADIUS server
Termination enabled:
EAP-TLS with CN lookup with external authentication server.
External Captive Portal clients using XML-API: PAP method.
MAC-based Authentication clients: PAP method.
How it Works :
Auth-Survivability can be enabled/disabled at each controller level and By default, it is disabled.
Two types of client auth info are saved in local mysql database when the associated client is authenticated.
- Client access credential
- Key reply attributes
Besides client Username, following data needs to be stored also:
- For PAP users, authmgr stores the encrypted SHA-1 hashed value of the password.
- For EAP-TLS 802.1x with termination disabled , an indicator of “EAP-TLS” is stored.
- For CN lookup, an indicator of “EXIST” is stored.
Store user auth info to survival cache under the following conditions:
- Client MAC address can not be all Zero.
- For EAP-TLS clients, issuer certificate of the Survival server certificate has to be installed as TrustedCA certificate in the client stations.
- For EAP-TLS clients with termination disabled, issuer certificate for the client certificate must be imported as TrustedCA or intermediateCA certificate at the controller.
A local Survival Server starts authenticating clients in the following situations:
- Survival server consists of a free radius server plus mysql database. It is configured to accept RADIUS requests from local host and retrieve access credential and Key reply attributes from the mysql database
- when all servers in the server group are out of service if fail-through is disabled.
- Or all in-service servers failed the authentication and at least one server is OOS when fail-through is enabled.
- All access credential and key reply attributes will be expired within the configured cache lifetime. By default, it is 24 hours.
- A cached entry will be deleted from local Survival Server in the following situations:
- When a station fails the authentication with an external server with fail-through disabled.
- Or when a station fails the authentication with all the external servers with fail-through enabled.
- All expired entries will be purged every 10 minutes.
How to configure:
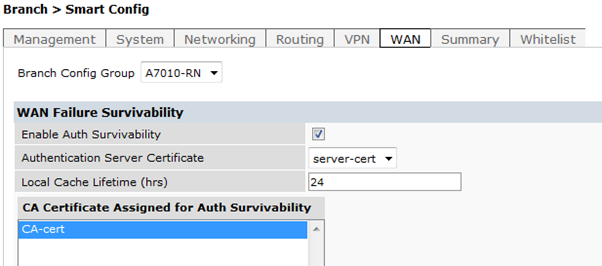
- Navigate to Configuration->Branch->SmartConfig->WAN Tab
- Select the branch-config-group which needs to be configured.
How to verify :
(A7010-1) #show aaa auth-survivability
Auth-Survivability: Enabled (Running)
Survival-Server Server-Cert: server-cert
Survival-Server Cache lifetime: 24 hours
# show aaa auth-survivability-cache
Auth-Survivability Cached Data
------------------------------
Station User Name Authenticated Using Authenticated By Authenticated On
------- --------- ------------------- ---------------- ----------------64:27:37:7F:BC:34 test1 PAP RadServer1 2014-04-01 01:54
64:27:39:AF:BC:F0 vpnclientcert2K-xyz EAP-TLS RadServer2 2014-04-01 18:21
To Clear Cached Information in the local Survival Server
# clear aaa auth-survivability-cache station 12:34:56:79:01:34 username test-00065844
1 entries are deleted from Survival Cache
# clear aaa auth-survivability-cache all
Survival Cache is cleared
What are the logs available
Auth survival logs are all under SECURITY.logs
#logging level debug security process survival
#logging level debug security process authmgr subcat aaa