You can create two custom attributes in the endpoint repository to handle this. This is a common deployment method.
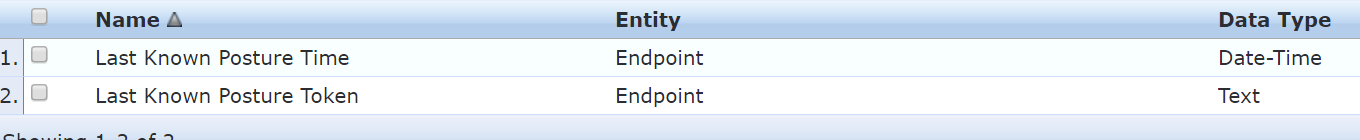
Here's the two attributes (you can change the names):
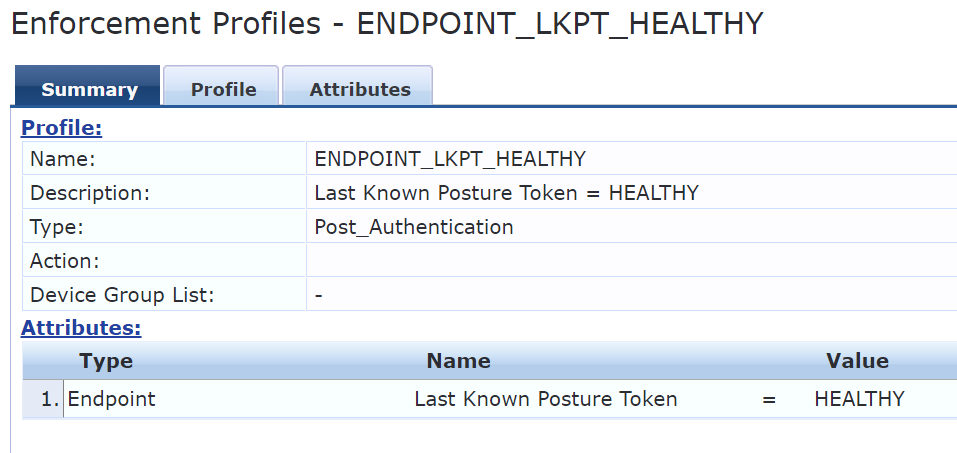
Create a few endpoint update enforcement profiles for each health status:
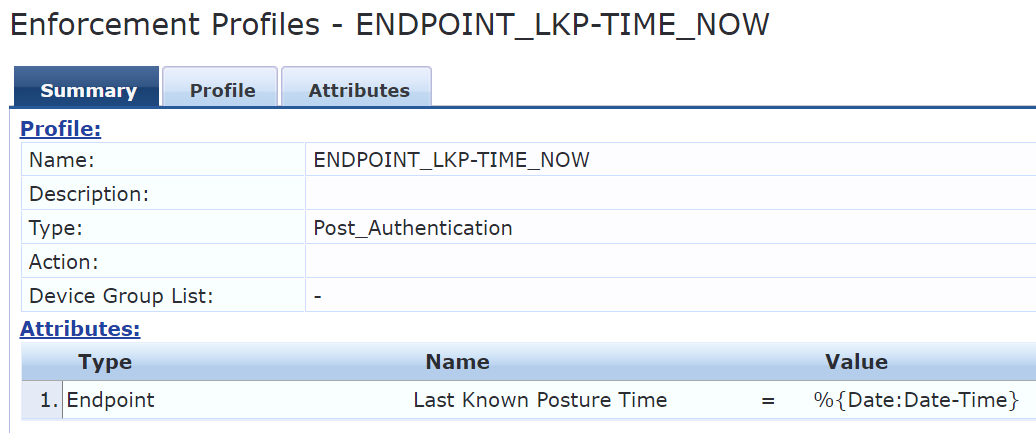
Create an endpoint update enforcement profile that stamps the current time:
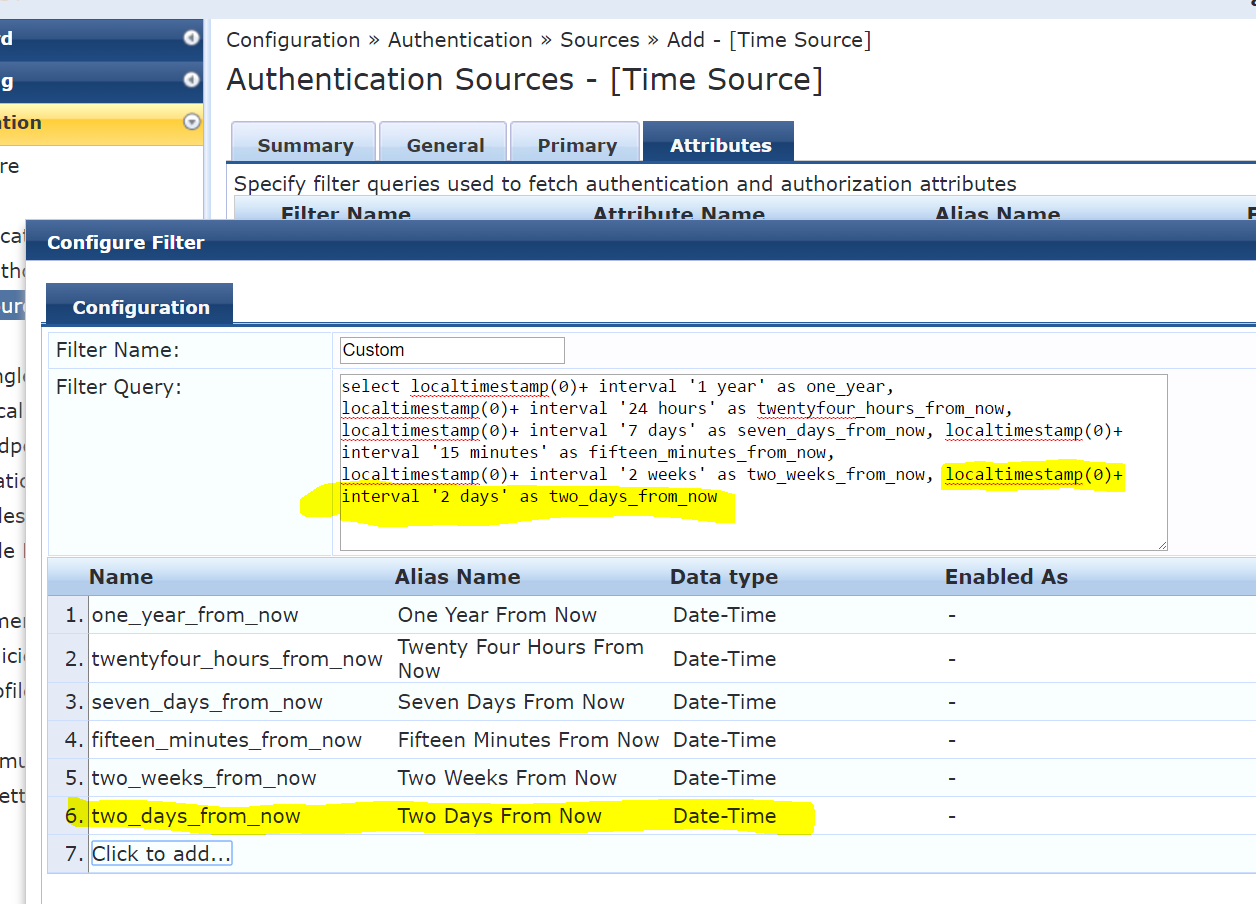
Now, you'll need to create a time attribute in [Time Source] that is your acceptable window for a valid posture token. In this example, it's two days:
Now to put it all together, in your Health Check WebAuth service, add the two Last Known X enforcement profiles to each rule (the time one should be added to all of them and you'll want to switch between the correct posture token depending on the rule).
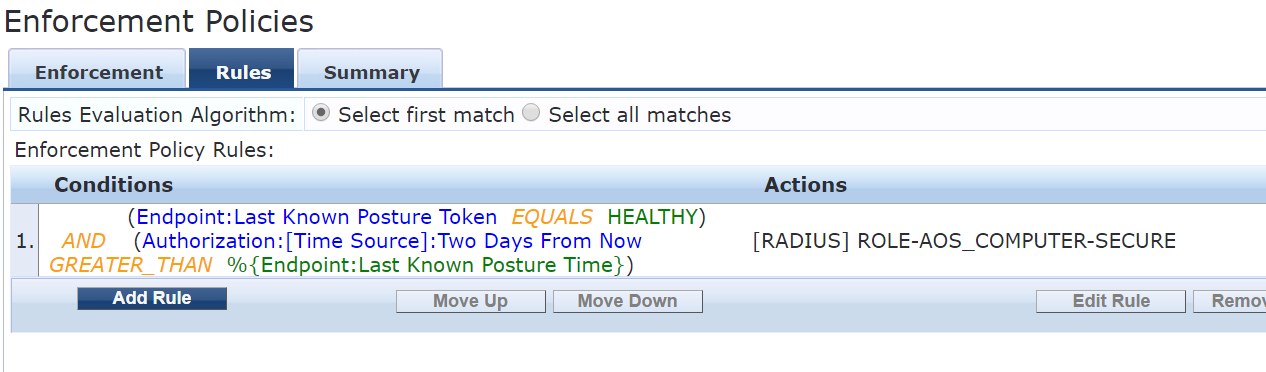
Now in your authentication service, you can do something like this:
Be sure [Endpoints Repository] and [Time Source] are added as authZ sources.