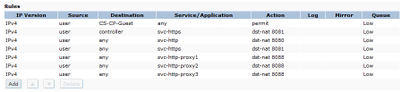
Your rules definitely look odd, try reverting them back to basics and see if it works.
The 1st rule needs to allow traffic from the user to your ClearPass server(s). You can use netdestinations as you did, either for any type of traffic or HTTPS/HTTP only (btw you could consolidate this in your policy by using 'svc-web' instead).
The following rules trigger any HTTPS/HTTP connection from the client to do a dst-nat on port 8081/8080 which is the controllers internal webserver:
If your logon-role has a captive portal profile assigned, the controller will redirect the client to whatever you configured in the captive portal profile and not to the controller's own internal captive portal.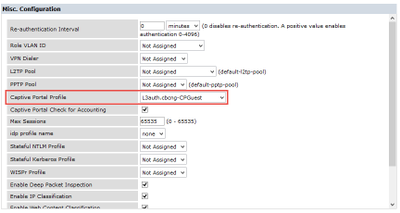
There is a bit older technote on AOS + Guest, which dicusses these basic workflows: https://community.arubanetworks.com/aruba/attachments/aruba/aaa-nac-guest-access-byod/27453/1/AOS_GuestAcccess-AppNote.pdf
Those mechanisms are still valid, independent from the AOS version us use.
In terms of certificates please closely follow cappalli's recommendations and have two separate public signed certificates.