Hi,
Good morning.
Start reading here:
http://community.arubanetworks.com/t5/Unified-Wired-Wireless-Access/Aruba-Mobility-Controller-integration-to-Free-RADIUS-on-Linux/td-p/93092
Trobuleshooting: (After u have configured everything on the controller and on your radius - NAS IP , SECRET,CERT on client machince <> on radius server )
------------------
1. Check that u have connectiviy - use diagnsotic - check aaa
2. Check logs in your Radius server
3.Be sure that port 1812/1813 are open between your radius and your controller
-----------------
how to config on contoller?
-----------------
http://www.arubanetworks.com/techdocs/ArubaOS_60/UserGuide/802.1x.php
The following steps demonstrate how to enable the 802.1x local terminatoin with eap-eap/eap-mschapv2. Please modify it with you desired EAP type.
1. Navigate to Configuration → Security → Authentication → servers → server group. Create a new server group if you are using external server for 802.1x authentication, and click Add. Click the server group you have just created and enter the server details.
2. Navigate to Configuration → Security → Authentication → L2 Authentication → 802.1x Authentication Profile → Create a profile → Add → Apply.
3. Select the profile that you have just created under 802.1x Authentication profile. Click → Advanced → Termination EAP-Type → check the eap-peap and eap-mschapv2 → Apply.
Note: ONLY , If you are using the internal server for 802.1x authentication, click the basic and check the termination option and click Apply.
4. Click the AAA profile tab. Under AAA Profiles Summary → Create a profile → Apply.
5. Click the profile you have just created under AAA profile → 802.1x Authentication Profile → choose the profile that you have created under L2 Authentication in step 2.
6. Click the AAA profile → 802.1x Authentication Server Group → select the server group from the drop-down menu → Apply.
7. Navigate to Configuration → Wireless → AP Configuration → Choose the AP group → edit → Wireless LAN → Virtual AP → Default → AAA profile → under Profile details, from the drop-down menu, select the AAA profile that you created in step 4 → Apply.
8. Click the SSID profile > Basic tab → Select the WPA encryption in network authentication → Apply.
------------------------------
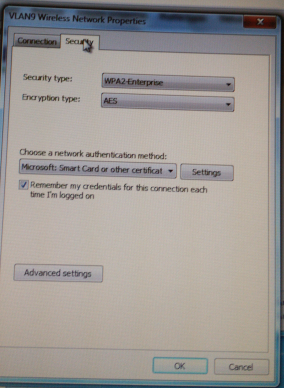
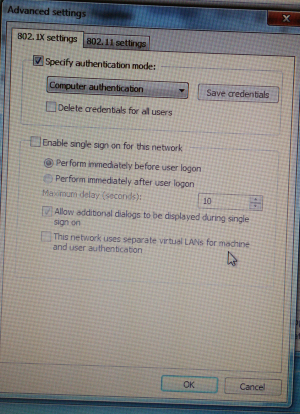
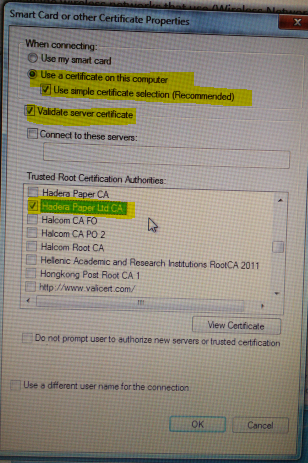
Here 3 screenshots of config tips for the wi-fi client itself:
------------------------------