Requirement:All the internet search providers have now switched to using HTTPS (encrypted) for all communications to their engines, it is no longer possible to look into the clear text of the request from the client and alter the request to force the search engines to return content and images suitable for display at work or in schools.
When the search results are displayed the pages for images and videos frequently have thumbnail pictures which could be unsafe for children or the work place.
It is not possible to block these thumbnail images or videos as these are returned directly from google over the encrypted channel - but clicking on them would then launch to the website which can be blocked by conventional firewalls or content firewalls.
So the aim of this article is to inform how to force the search providers not to send these thumbnail images in the first place - this is called Safe Search.
It is possible to manually configure each client to enable 'Safe Search' but for obvious reason this is not workable when there are thousands of devices, and what about the BYOD devices - configuring these is something which is just not possible.
So Google recognize this is a significant issue and have come up with another way which is to change any request to 'google' to get a DNS response forcing the client to forcesafesearch.google.com traffic to forcesafesearch.google.com does exaclty what it says always returns safe search content.
Google has over 190 DNS TLDs so each one has to redirected.
Google have also implemented the same for You Tube - forcing it to 'restricted mode' - restrict.youtube.com (note same VIP as forcesafesearch.google.com)
Bing have also followed suit and they have a Safe Search VIP - strict.bing.com
Yahoo as far as I can tell do not support DNS mapping to a Safe Search VIP.
Solution:Although the controller does not have a DNS server and its not possible to re-write DNS requests forcing to the safesearch VIP's, It is possible to listen to these DNS requests and responses and then use an ACL to look for the destination IP addresses.
The solution is to configure netdestinations and then to apply these destinations to ACL rules which can then destination NAT to the 'Safe Search' VIP.
Google
forcesafesearch.google.com = 216.239.38.120
You Tube
restrict.youtube.com = 216.239.38.120
Bing
strict.bing.com = 204.79.197.220
Configuration:The configuration requires that the controller has the PEFNG license installed.
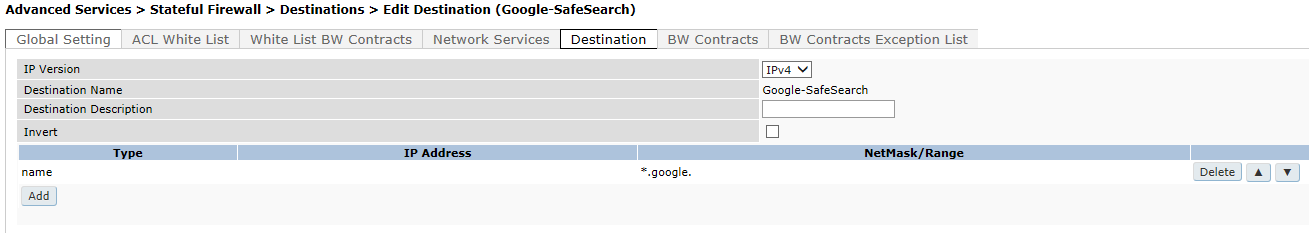
From the WebUI create the following 'Destinations'
Google;
You Tube

Bing;

Then create a policy and create the following rules

Then apply this policy to the users authenticated role.
Example from the CLI;
netdestination Bing-SafeSearch
name www.bing.com
!
netdestination Google-SafeSearch
name *.google.
!
netdestination YouTube-restricted
name www.youtube.com
name m.youtube.com
name youtubei.googleapis.com
name youtube.googleapis.com
name www.youtube-nocookie.com
name www.googleapis.com
!
ip access-list session SafeSearch
any alias YouTube-restricted any dst-nat ip 216.239.38.120
any alias Google-SafeSearch any dst-nat ip 216.239.38.120
any alias Bing-SafeSearch any dst-nat ip 204.79.197.220
!
user-role authenticated
access-list session global-sacl
access-list session apprf-authenticated-sacl
access-list session SafeSearch
access-list session ra-guard
access-list session allowall
access-list session v6-allowall
!
VerificationTo verify the configuration it is possible to view the DNS name to IP mapping on the controller and viewing the session table it is possible to see the destination NAT sessions.
(Aruba3200) #show firewall dns-names
FW DNS names
------------
Name Id InUse List
---- -- ----- ----
*.google. 13 1 216.58.213.174 216.58.213.163
youtube.googleapis.com 9 1
m.youtube.com 7 1
accounts.google.com 1 1
www.youtube.com 6 1 64.233.167.91 64.233.167.93 64.233.167.136 64.233.167.190
graph.facebook.com 3 1
www.bing.com 12 1 204.79.197.200
www.youtube-nocookie.com 10 1
ssl.gstatic.com 2 1 216.58.213.163
youtubei.googleapis.com 8 1
www.googleapis.com 11 1 216.58.213.138
facebook.com 5 1
fbstatic-a.akamaihd.net 4 1
(Aruba3200) #
(Aruba3200) #show datapath session table 192.168.254.252
Datapath Session Table Entries
------------------------------
Flags: F - fast age, S - src NAT, N - dest NAT
D - deny, R - redirect, Y - no syn
H - high prio, P - set prio, T - set ToS
C - client, M - mirror, V - VOIP
Q - Real-Time Quality analysis
I - Deep inspect, U - Locally destined
E - Media Deep Inspect, G - media signal
r - Route Nexthop
Source IP Destination IP Prot SPort DPort Cntr Prio ToS Age Destination TAge Packets Bytes Flags
--------------- --------------- ---- ----- ----- -------- ---- --- --- ----------- ---- --------- --------- ---------------
192.168.254.254 192.168.254.252 17 53 64288 0/0 0 0 0 tunnel 10 1 1 242 FI
192.168.254.252 192.168.254.254 17 64288 53 0/0 6 0 1 tunnel 10 1 1 61 FCI
192.168.254.252 216.58.213.163 6 49411 443 0/0 0 0 0 tunnel 10 2 72 7650 NC
192.168.254.252 216.58.210.67 6 49412 443 0/0 0 0 0 tunnel 10 1 21 2104 NC
216.239.38.120 192.168.254.252 6 443 49411 0/0 0 0 0 tunnel 10 2 60 34224 S
216.239.38.120 192.168.254.252 6 443 49412 0/0 0 0 0 tunnel 10 1 17 5776 S
(Aruba3200) #
We can see that DNS requests are marked for Deep inspection (I) and data going to google is being Destination NAT'd (N)