Hi,
You can do it in multiple ways as explained below depending on your preference..
1) You can use vlan name and return the name of the vlan instead of ID. As such, your policy will be simplified. You will always for example return vlan EMPLOYEE where on switch 1 vlan EMPLOYEE means vlan 51 while on switch 2 it means 52...etc. The same vlan name needs to be properly configured on your switches..
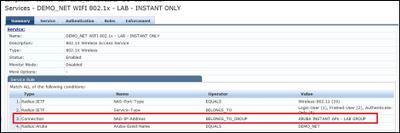
2) You can use Service rules to match a request to a particular service..In your service you restrict it based on NAD_IP_ADDRESS BELONGS_TO_GROUP.. You will need to create multiple service rules in this case matching the different groups. Each service rule will have its own enforcement policy..
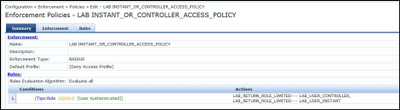
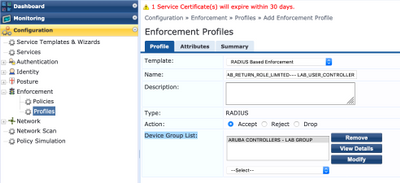
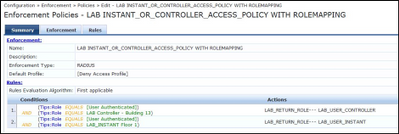
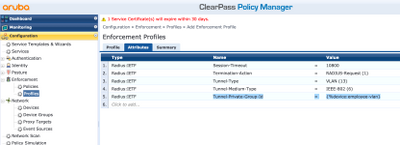
3) You can use one service rule and use Enforcement Policies to only apply the relevant enforcement profile if the originating request belongs to a device in the group. In your policy, you will have multiple enforcement profiles associated with the same rule however the trick here is that the enforcement profile itself is restricted to a particular device group. ClearPass is intelligent enough to only apply the relevant enforcement profile matching the request..
The trick is when you create the profile, you associate it with a particular device group.
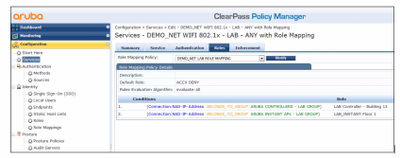
4) You can use Role mapping rules to map a request to a particular role and then apply the needed logic in your enforcement policy based on the role mapping..
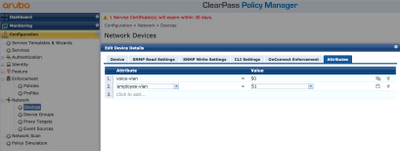
5) You can use device attributes once you add the network device. And in your policy, you can assign the vlan using {%device:attribute-name}
For example, for the below screenshot, I can use {%device:employee-vlan} which will automatically replace the employee-vlan with the associated vlan set in the device attributes..
I hope I didn't confuse you with all of the above options but I really love the flexibility of ClearPass!