Hi all,
we've set up the ClearPass Policy Manager to control access to our WLAN networks via WPA2 Enterprise and RADIUS. So far it is working fine with local users.
Now we want to set up a connection to Office 365 because there we have all users that should be able to connect to the WLANs. Setting up local users on the ClearPass manually would become superfluous.
The first idea we've had was to set up secure LDAP service as described here:
Configure secure LDAP (LDAPS) for an Azure AD Domain Services managed domain
The integration under "Authentication --> Sources" was successfully and were able to browse through the directory and set up filters:
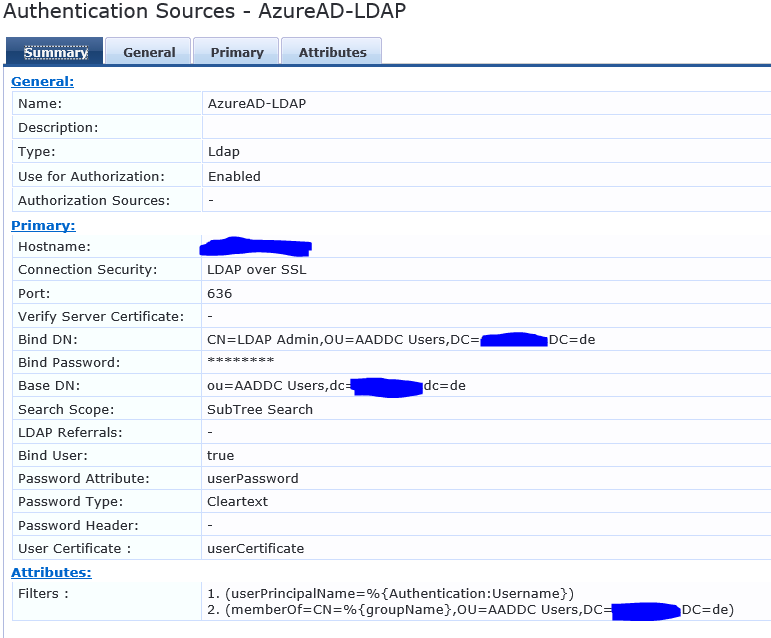
With the second filter we control if the user is in the right group (users that are allowed to connect to the WLAN are assigned to a special group in Azure AD).
After that we've updated the role mapping:
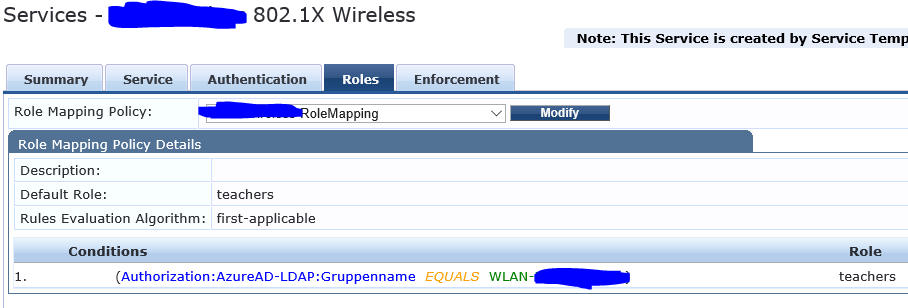
("Gruppenname" stands for "group name")
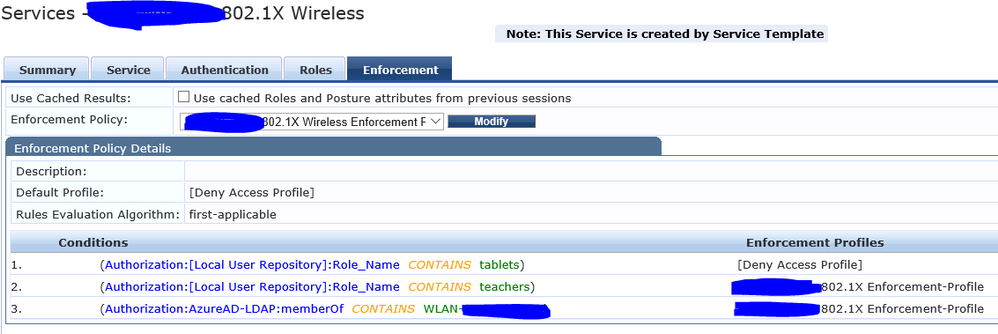
... and the enforcement policy:
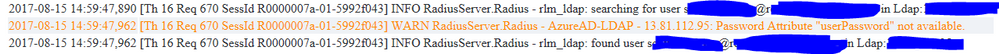
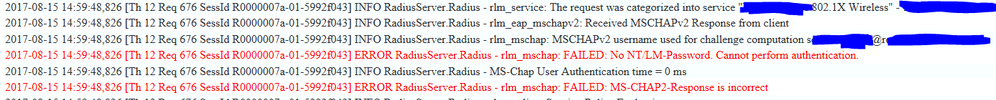
Now we've tried to log in via the Office 365 credentials, but they are rejected all time. The log shows the following errors:
Is there a mistake in our configuration? Or isn't it possible to adopt Azure AD via LDAP at all?
Connecting directly to AD isn't a option because we don't have a local server that is syncing with Azure AD. Also the the integration of a social login is not looking suitably for our needs. Do you have some other ideas?
Thanks a lot!