As Seth pointed out this happens when it is a new device and ClearPass has not learned or profiled before
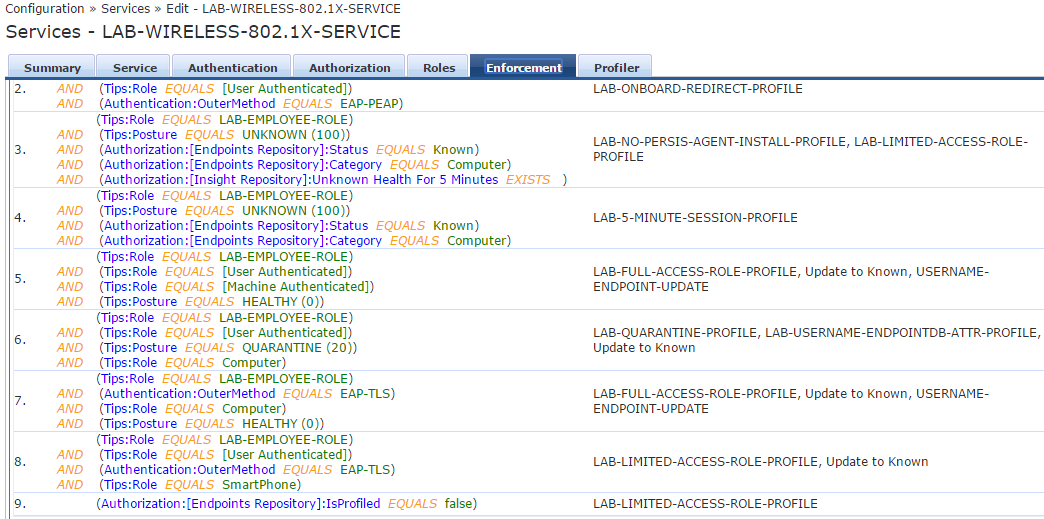
So if you are making policy decisions based on the profile information from the endpoint database the first time the device connects it won't hit any of the rules of your enforcement policy .
What you need to do is the following :
You need to add a catch all rule that if the device hasnt been profiled it will be allowed to get DHCP for brief time and then the device will get CoA and then next time it comes through it will hit whatever the rule you specified.
In order for this to work you need to configure ClearPass as DHCP relay and as cappalli said you need to add the endpoint DB as your authorization source