HTTP GUI Access
A customer asked about access to one of the older ProCurve 2520 switches. This applies to many of the switches from a similar timeframe; I tested a 2520 and 5406zl (V1 chassis).
Both switches have the most recent firmware. The 2520 used in this post has a basic config:
; J9298A Configuration Editor; Created on release #J.15.09.0028
; Ver #06:04.08.00.01.14.05:1a
hostname "HP-2520G-8-PoE"
ip default-gateway 10.20.30.1
snmp-server community "public" unrestricted
vlan 1
name "DEFAULT_VLAN"
no untagged 1
untagged 2-10
no ip address
exit
vlan 930
name "VLAN930"
untagged 1
ip address dhcp-bootp
exit
password manager
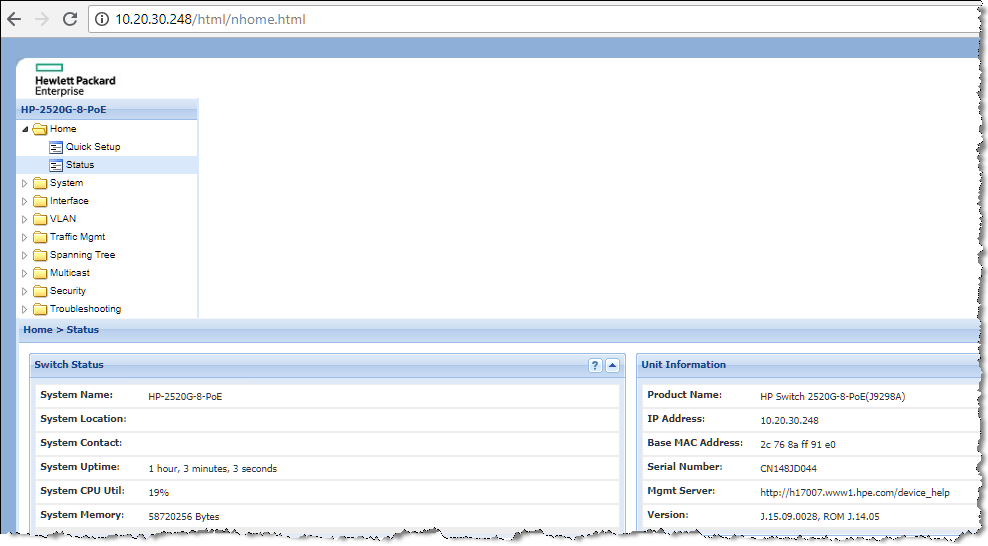
To browse with HTTP (port 80), you don't have to do anything - it works straight out of the box, just like SSH!
HTTPS/SSL GUI Access
To enable SSL access (HTTPS, port 443) is a little more involved. Also note that only older ciphers are used, and may not work with current browsers and/or settings (more on that at the end).
Set the time! Nothing cryptographic works unless the time is set. Ideally you should use timesync (such as SNTP in these older switches).
web-management ssl is the key command; it will remind yuo to install the certificate first.
HP-2520G-8-PoE(config)# web-management ssl
https cannot be enabled with no certificate present. To install a
self-signed certificate,
* Use 'crypto key generate...' to install RSA key; then
* Use 'crypto host-cert generate...' to install certificate.
HP-2520G-8-PoE(config)# crypto key generate cert rsa bits 2048
Installing new key pair. If the key/entropy cache is
depleted, this could take up to a minute.
HP-2520G-8-PoE(config)# crypto host-cert generate self-signed
Validity start date [07/20/2018]:
Validity end date [07/20/2019]: 07/20/2029
Common name [0.0.0.0]: 10.20.30.248
Organizational unit [Dept Name]: Aruba
Organization [Company Name]: HPE
City or location [City]: Sydney
State name [State]: NSW
Country code [US]: AU
HP-2520G-8-PoE(config)# web-management ssl
The GUI should now be accessible via https:// - except it isn't... Doesn't work on current versions of Chrome or Firefox.
I found an old version of IE (v11 from 2013) on an old machine, and it worked fine:
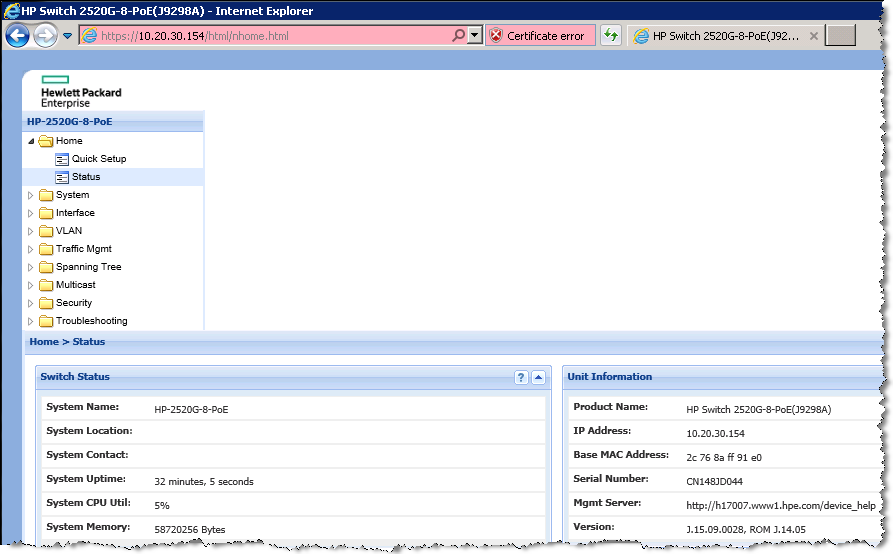
A Wireshark capture confirms that an old version is used, in this case TLSv1.0
Enabling Old Versions
This is not a good idea. However, if you are particularly keen, you can enable Firefox to use a specific version - in this case TLS1.0. Don't forget to change it back afterwards!
Type in about:config on the Firebox browser line, and change the blue highlighted settings to 1 (the number for TLSv1.0).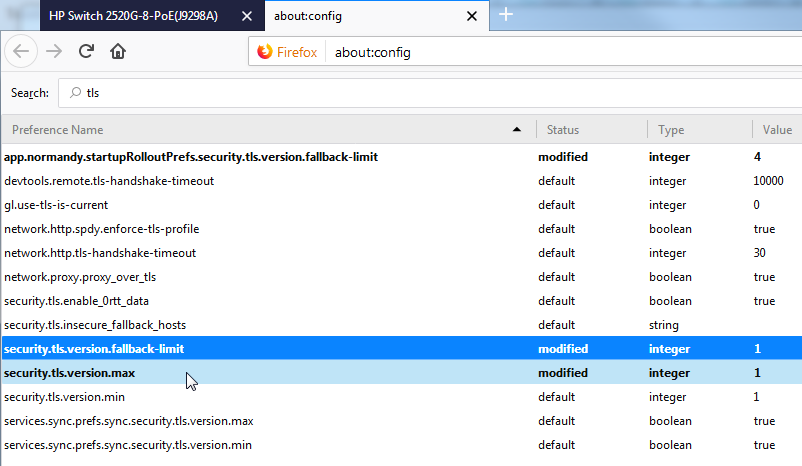
It now works in Firefox:
Other Notes
You can delete the cert with:
crypto key zeroize cert
Once you have a self-signed cert installed, you can add a proper CA-signed cert from the GUI.