SNMP is about the most common way to monitor and manage network devices, including switches.
Best Practice
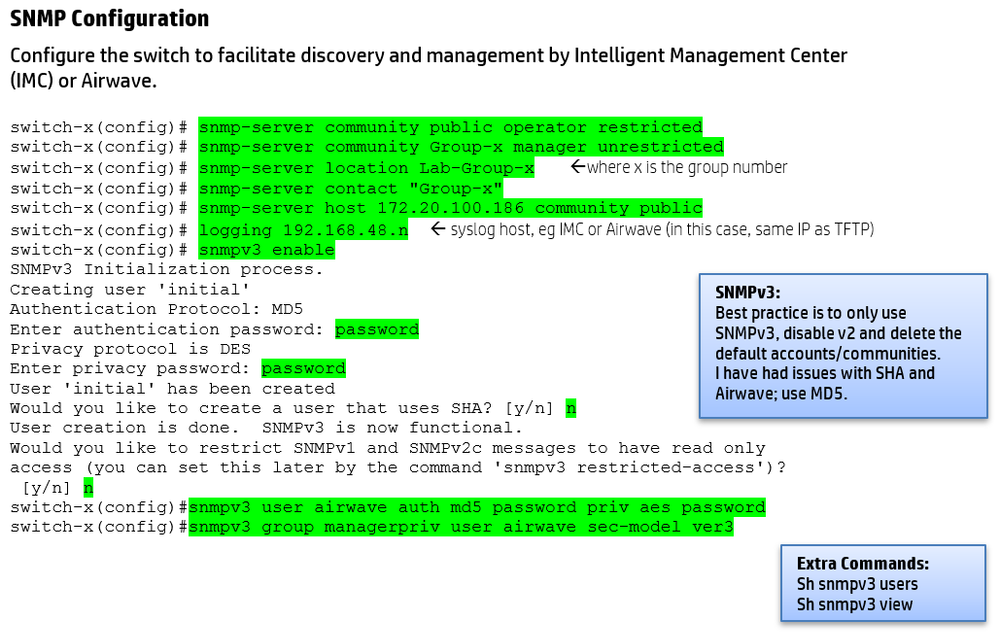
Ideally, you should be using SNMPv3 because SNMPv2 is not secure - the community strings are transmitted in clear text. However, SNMPv2 still seems to be pretty common (it is a little easier to setup), so both options are provided below.
Best practice is to only use SNMPv3, disable v2 and delete the default accounts/communities. I have had issues with SHA and Airwave; I suggest the use of MD5.
SNMPv2 Configuration
switch-x(config)# snmp-server community public operator restricted
switch-x(config)# snmp-server community Group-x manager unrestricted
switch-x(config)# snmp-server location Lab-Group-x
switch-x(config)# snmp-server contact "Group-x"
switch-x(config)# snmp-server host 172.20.100.186 community public
SNMPv3 Configuration
switch-x(config)# snmpv3 enable
SNMPv3 Initialization process.
Creating user 'initial'
Authentication Protocol: MD5
Enter authentication password: password
Privacy protocol is DES
Enter privacy password: password
User 'initial' has been created
Would you like to create a user that uses SHA? [y/n] n
User creation is done. SNMPv3 is now functional.
Would you like to restrict SNMPv1 and SNMPv2c messages to have read only
access (you can set this later by the command 'snmpv3 restricted-access')?
[y/n] n
switch-x(config)#snmpv3 user airwave auth md5 password priv aes password
switch-x(config)#snmpv3 group managerpriv user airwave sec-model ver3
Useful Commands
sh run | in snmp
sh snmpv3 users
sh snmpv3 view
Notes
This is an extract from the training course I updated in Jun 2018
These commands are applicable to the ArubaOS-Switch devices, and many of the precursor devices (ProCurve, E Series)