Requirement:
How to configure dynamic server selection?
Solution:Managed devices can dynamically select an authentication server from a server group based on the user information sent by the client in an authentication request. For example, an authentication request can include client or user information in one of the following formats:
- <domain>\<user>: for example, corpnet.com\darwin
- <user>@<domain> : for example, darwin@corpnet.com
- host/<pc name>.<domain> : for example, host/darwin-g.finance.corpnet.com (this format is used with 802.1X machine authentication in Windows environments)
When you configure a server in a server group, you have the option to associate the server with one or more match rules. A match rule for a server can be one of the following:
- The server is selected if the client/user information contains a specified string.
- The server is selected if the client/user information begins with a specified string.
- The server is selected if the client/user information exactly matches a specified string.
We can configure multiple match rules for the same server. Managed devices compare the client/user information with the match rules configured for each server, starting with the first server in the server group. If a match is found, the managed device sends the authentication request to the server with the matching rule. If no match is found before the end of the server list is reached, an error is returned, and no authentication request for the client/user is sent.
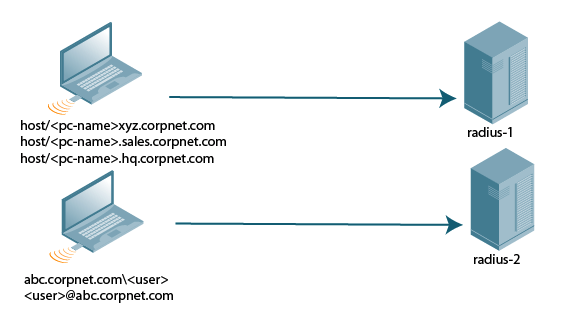
Image below depicts a network consisting of several subdomains in corpnet.com. The server radius-1 provides 802.1X machine authentication to PC clients in xyz.corpnet.com, sales.corpnet.com, and hq.corpnet.com. The server radius-2 provides authentication for users in abc.corpnet.com.
Configuration:(host) [mynode] (config) #aaa server-group auth-server [match-authstring contains|equals|starts-with ] [match-fqdn ] [position ] [trim-fqdn]
Verification#show auth-tracebuf mac 54:13:79:11:21:eb
May 3 13:37:47 station-up * 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 - - wpa2 aes
May 3 13:37:47 eap-id-req <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 1 5
May 3 13:37:47 eap-id-resp -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 1 17 host/NCHAM0982.corpnet.com
May 3 13:37:47 rad-req -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 173 182
May 3 13:37:47 rad-resp <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11/Radius1 173 90
May 3 13:37:47 eap-req <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 2 6
May 3 13:37:47 eap-resp -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 2 216
May 3 13:37:47 rad-req -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11/Radius1 174 419
May 3 13:37:47 rad-resp <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11/Radius1 174 243
May 3 13:37:47 eap-req <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 3 159
May 3 13:37:47 eap-resp -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 3 69
May 3 13:37:47 rad-req -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11/Radius1 175 272
May 3 13:37:47 rad-resp <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11/Radius1 175 191
May 3 13:37:47 eap-req <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 6 107
May 3 13:37:47 eap-resp -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 6 107
May 3 13:37:47 rad-req -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11/Radius1 176 310
May 3 13:37:48 rad-accept <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11/Radius1 176 292
May 3 13:37:48 eap-success <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 6 4
May 3 13:37:48 wpa2-key1 <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 - 117
May 3 13:37:48 wpa2-key2 -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 - 117
May 3 13:37:48 wpa2-key3 <- 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 - 151
May 3 13:37:48 wpa2-key4 -> 54:13:79:11:0f:5f 24:f2:7f:e1:e8:11 - 95
User 2:
#show auth-tracebuf mac 54:13:79:07:3c:7d
May 3 13:40:02 station-up * 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 - - wpa2 aes
May 3 13:40:02 eap-id-req <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 1 5
May 3 13:40:02 eap-start -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 - -
May 3 13:40:02 eap-id-req <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 1 5
May 3 13:40:02 eap-id-resp -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 1 17 Corpnet\Test
May 3 13:40:02 rad-req -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 185 182
May 3 13:40:02 eap-id-resp -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 1 17 Corpnet\Test
May 3 13:40:02 rad-resp <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11/Radius2 185 90
May 3 13:40:02 eap-req <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 2 6
May 3 13:40:02 eap-resp -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 2 216
May 3 13:40:02 rad-req -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11/Radius2 186 419
May 3 13:40:02 rad-resp <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11/Radius2 186 243
May 3 13:40:02 eap-req <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 3 159
May 3 13:40:02 eap-resp -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 3 69
May 3 13:40:02 rad-req -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11/Radius2 187 272
May 3 13:40:02 rad-resp <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11/Radius2 187 191
May 3 13:40:02 eap-req <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 6 107
May 3 13:40:02 eap-resp -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 6 107
May 3 13:40:02 rad-req -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11/Radius2 188 310
May 3 13:40:02 rad-accept <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11/Radius2 188 292
May 3 13:40:02 eap-success <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 6 4
May 3 13:40:02 wpa2-key1 <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 - 117
May 3 13:40:02 wpa2-key2 -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 - 117
May 3 13:40:02 wpa2-key3 <- 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 - 151
May 3 13:40:02 wpa2-key4 -> 54:13:79:07:3c:7d 24:f2:7f:e1:e8:11 - 95