This is what you can do:
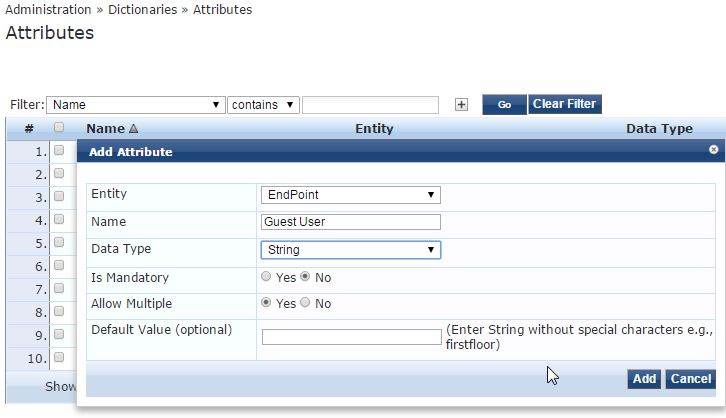
- First create a custom attribute
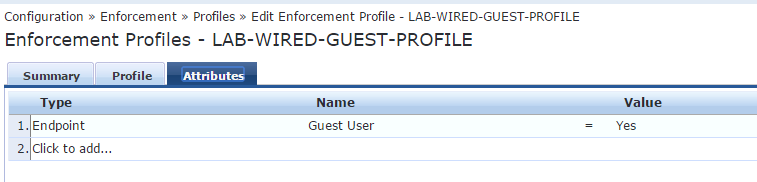
- Then create a post_authentication enforcement profile using this custom attribute
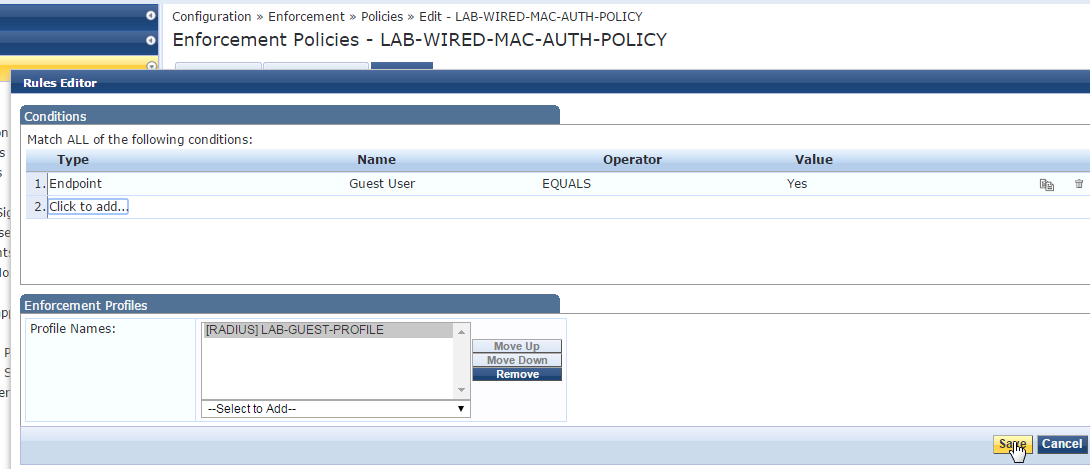
- On the enforcement policy of your webauth include the Cisco terminate to CoA the device and also add the post_authentication custom attribute so you can use later on your MAc auth to provide access to the guest user
See if this helps you.
Note: You may need to add 10-25 seconds delay in the weblogin to allow the whole process(CoA, Mac,etc..) to work properly