Imagine a campus network with a few thousand switch access ports, numerous intermediate distribution frames (IDFs) with redundant uplinks to core switches and the usual connected devices like PCs, Access Points, IP cameras, phones, physical access devices and so on.
The basic MAC (MoveAddChange) effort requires a good amount of work for network administrators each day.
Now imagine having to install the whole network and connect devices to all switch ports in one week and have it shipped in the middle of the ocean.
This scenario needs a very detailed and difficult to maintain switch port to VLAN mapping (a.k.a. a spreadsheet file) and a big configuration effort to manage thousands if lines of configurations on the switches.
It is easy to understand this way to manage the network is error prone and requires changes every time a device moves.
A COLORLESS WORLD
Let's imagine a different scenario now where all switch ports are colorless and every access port gets its configuration based on the connected device.
All the switches would have similar configuration with IP, credentials, authentication, VLANs and uplinks. All access ports need only a few lines of configuration common for all ports.
Welcome to the colorless world.
FIAT PIGMEMTUM
A colorless worls is quite boring, What creates color in a colorless world is the authentication back-end managed by Aruba ClearPass.
ClearPass can identify clients connected to switch ports based on 802.1x credentials, mac-auth, Captive Portal and more.
Using mac-auth is much simpler and one of the fastest methods in an environment where there are limits on the client capabilities. The focus here is not security per se but speed of deployment and being sure every devices is assigned to the correct VLAN.

SHARPENING THE AXE
The preparation phase for this kind of delivery is crucial. It's very important to retrieve the list of all the devices that will be connected to the network in advance, in particular the mac-address list or at least the MAC OUI. This is possible in a controller environment where most devices are known.
ClearPass supports the profiling of devices based on vendor OUI or the specific mac-address. Each OUI or MAC will then be associated to its VLAN by a Policy.
With these two elements, identification/profiling and policy/enforcement, the deployment phase is just a matter of physical installation and patching.
DEPLOYMENT PHASE
Once every switch is racked and powered devices can be connected to any port. The mac-auth feature sends and authentication and authorization request to ClearPass. The authorization in response allows the device to connect and assigns the switchport to the correct VLAN.
At the first connection, the mac-address of the device may not be in the internal ClearPass database so the initial profiling phase must be performed. The device mac address is matched against the vendor OUI, a new entry in the internal database is created for the specific device. In addition, a RADIUS CoA message is sent to the switch to authorize and move the siwtch port to the correct VLAN. It actually takes just a few seconds for new devices and the second time the process is almost immediate.
Compare this process to any manual/static VLAN implementation and the advantages are quite clear. There's no chance of error if the initial creation of policies is correct. Incorrect VLAN assignments are easy to spot and fix, ClearPass logs all the accesses and assigned profiles.
For new/unknown devices manual profiling is requires but the process is straightforward. Once a new unprofiled device is connected ClearPass will assign it to a DMZ VLAN and it will be listed. It only needs a few clicks to assign the device to a profile and have it assigned to the correct VLAN. This is much better and faster than asking the MAC address, searching it across multiple devices and configuring the switch port.
ADD SOME SPICE WITH DHCP PROFILING
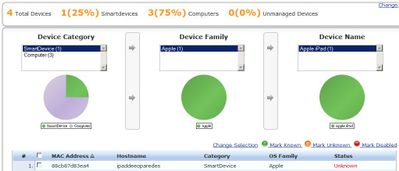
As a further method of end-point visibility, ClearPass can collect DHCP requests from clients and collect the include information. The Endpoint Profiler screen shows connected clients with fingerprint and attributes.
The configuration is quite straightforward, it only needs an DHCP relay (a.k.a. helper address) configured on the L3 switches.
DHCP packets received by ClearPass are decoded to extract the device category, name, hostname and IP address.
SECURITY CONSIDERATIONS
MAC address authentication is not and should not be considered a strong security feature. This method is vulnerable to spoofing attacks and provides no guarantee of device identity. A stronger auth method like 802.1x with client certificates should be used for environments where security is critical.
In the network design presented here mac-auth is used to provide a flexible campus configuration with a small administrative effort. Take in consideration all the aspects of this design before using it in your environment.
FURTHER READING
@cappalli's ClearPass Solution Guide is the best starting point and provides many details of the actual implementation.