It is expected that you only get the root, the intermediates are sent during the SSL session-setup by the ClearPass. So, no need for any intermediates to be installed on the switch. The 'good thing' about using that well-known-URL is that you always get the correct certificate, it now seems that there is something wrong with that root.
Can you share your root CA cert as retrieved from ClearPass? I can try to import it in my switch and see what is possibly wrong.
In parallel, please open a case with Aruba TAC support if you need a prompt resolution.
------------------------------
Herman Robers
------------------------
If you have urgent issues, always contact your Aruba partner, distributor, or Aruba TAC Support. Check
https://www.arubanetworks.com/support-services/contact-support/ for how to contact Aruba TAC. Any opinions expressed here are solely my own and not necessarily that of Hewlett Packard Enterprise or Aruba Networks.
------------------------------
Original Message:
Sent: Mar 16, 2021 04:16 PM
From: Brian Reed
Subject: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
Thanks for the reply!
When I view HTTPS Server Certificate I have the chain
Cert – Intermediate – Intermediate– Root
When I view the https-root.pem via the browser url and save as pem and view it is just the root. Maybe that's normal? But in AOS-CX it is showing "Installed, Malformed" but browsing via https the cert shows as ok.
Original Message:
Sent: 3/16/2021 3:59:00 PM
From: alagoutte
Subject: RE: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
Never...
you get the root certificate of HTTPS certificate (not the certificate of CPPM)
What CPPM release ?
------------------------------
PowerArubaSW : Powershell Module to use Aruba Switch API for Vlan, VlanPorts, LACP, LLDP...
PowerArubaCP: Powershell Module to use ClearPass API (create NAD, Guest...)
PowerArubaCX: Powershell Module to use ArubaCX API (get interface/vlan/ports info)..
ACEP / ACMX #107 / ACDX #1281
Original Message:
Sent: Mar 16, 2021 11:44 AM
From: Brian Reed
Subject: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
When I visit the /.well-known/aruba/clearpass/https-root.pem it doesn't actually show the same certificate that I'm using for HTTPS access on the Administration > Certificates > Certificate Store > HTTPS Server Certificate. It shows a different cert that is in my trust list. Have you seen that? Are there other options to download via a url than the "https-root.pem"? How does it know which cert to grab?
------------------------------
Brian Reed
Original Message:
Sent: Mar 08, 2021 11:40 AM
From: Herman Robers
Subject: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
Let's start by mentioning again that you should create your CPPM server certificate from Onboard only in lab environments. For production, get a certificate signed by a public root CA, or only if you don't use Guest and/or Onboard, from your corporate PKI.
This is specific for Downloadable User Roles, which have the requirement that the switch should know the root CA that signed your ClearPass HTTPS certificate. Side-note, this also means you cannot use a self-signed certificate in this case, public cert if recommended.
Then the second step is to install the 'trust anchor' certificate, which is the same as the root that signed your ClearPass HTTPS certificate, needs to be known at the switch. This is required to validate ClearPass when downloading the role which runs over HTTPS.
For AOS-CX you paste the certificate as shown above in the last part (installation on the switches).
ArubaOS Switches, and Instant APs will automatically download the certificate from ClearPass assuming you have fairly recent software versions (from top of my head CPPM 6.8+ and must be 16.08+ or so on the switch; just take CPPM 6.9.5 and 16.10 and it will work for sure).
What happens automatically is that the ClearPass Root CA will be downloaded over the URL: http://your-clearpass.domain/.well-known/aruba/clearpass/https-root.pem (replace your-clearpass.domain with the IP or fqdn of your ClearPass server). So, if you have recent software versions, it is not needed to do it.
For AOS-CX, I would recommend doing the same but manually:
- Download the root certificate to your computer from http://your-clearpass.domain/.well-known/aruba/clearpass/https-root.pem
- Open the downloaded pem file as text file (or copy the content from your browser)
- Run the commands mentioned above and use what you have in the text file to paste as the certificate.
The benefit of this approach is that this will always get the correct root CA, regardless if you had your ClearPass HTTPS certificate signed by a public CA (recommended) or private CA, or Onboard internal CA (deprecated, only use in labs where you can't do something else).
------------------------------
Herman Robers
------------------------
If you have urgent issues, always contact your Aruba partner, distributor, or Aruba TAC Support. Check https://www.arubanetworks.com/support-services/contact-support/ for how to contact Aruba TAC. Any opinions expressed here are solely my own and not necessarily that of Hewlett Packard Enterprise or Aruba Networks.
Original Message:
Sent: Mar 06, 2021 03:53 AM
From: Bruno Chirico
Subject: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
"Make sure your ClearPass HTTPS server cert is signed by the root cert authority whose certificate the switch will download."
How do you do this? by just downloading the onboard certificate like in the example above? I tried this but it does not seems to work. Or am i missing somthing?
Original Message:
Sent: Mar 05, 2021 05:42 PM
From: Justin Noonan
Subject: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
CX allows you to copy/paste the certificate contents.
With AOS-Switch you'll either need to upload it via tftp or you can use the automatic certificate download feature:
https://techhub.hpe.com/eginfolib/Aruba/16.09/5200-5908/index.html#GUID-6B4867D7-B72F-40B6-8012-8542725CCF7A.html
Make sure your ClearPass HTTPS server cert is signed by the root cert authority whose certificate the switch will download.
------------------------------
Justin Noonan
Original Message:
Sent: Mar 05, 2021 08:23 AM
From: Bruno Chirico
Subject: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
Hello
I have tried this with a 2930f switch but it does not seems to work.
Does this only work with the CX series?
i uploaded the certificate with the copy tftp command.
Do i need to change the https certificate in clearpass aswell?
Original Message:
Sent: Sep 01, 2020 07:14 AM
From: Yash NN
Subject: Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
Good day!
Simple Steps to create the HTTPS Server certificate on ClearPass for your Switches!
As may know, https server certificate is must for Downloadable User Role also known as DUR. Please see simple steps to generate https server certificate on Clearpass.
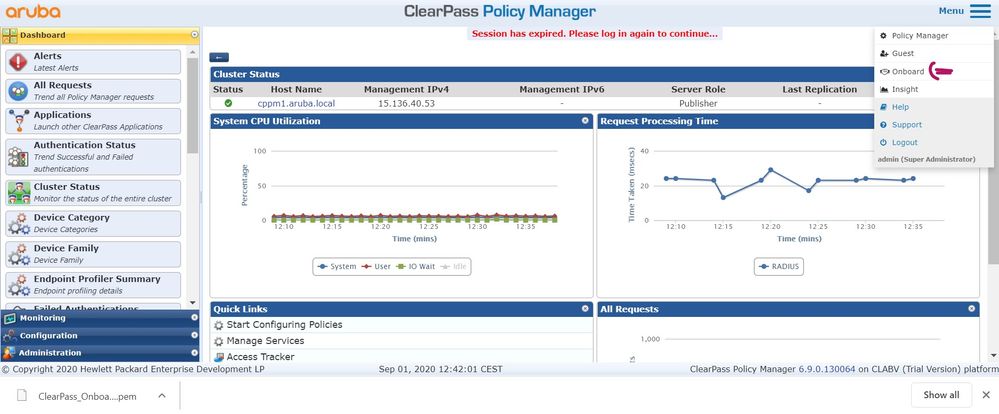
Step1: login to clearpass policy manager
 login to clearpass policy manager
login to clearpass policy manager
Step2: Click on Menu (right side corner) and then click onboard as below
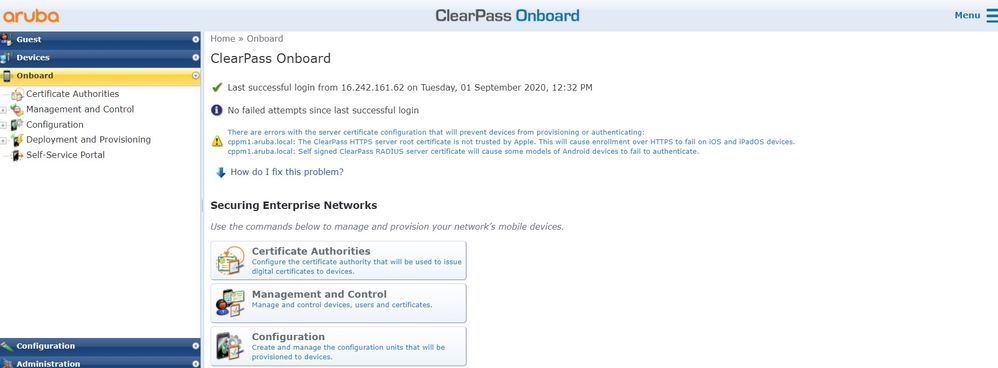
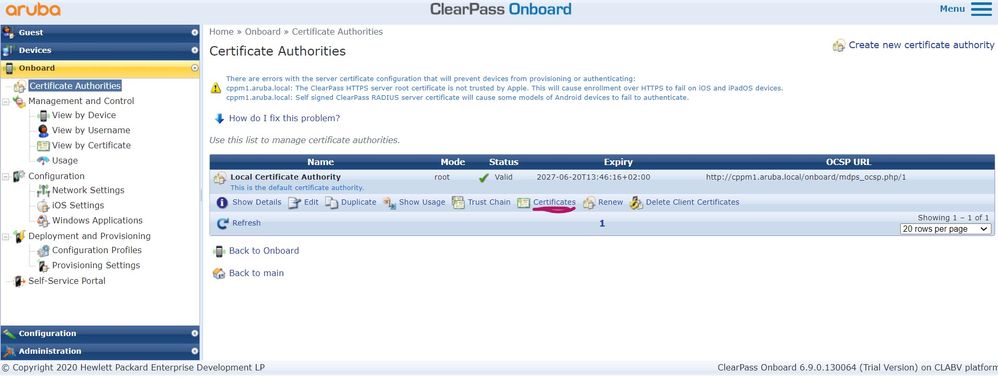
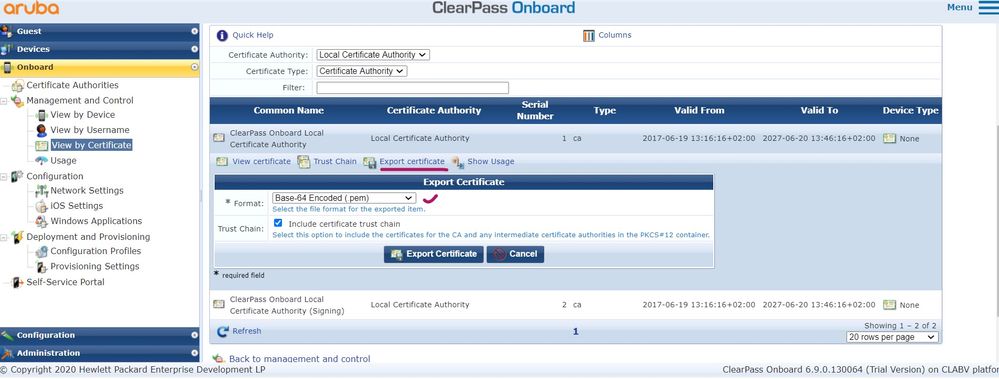
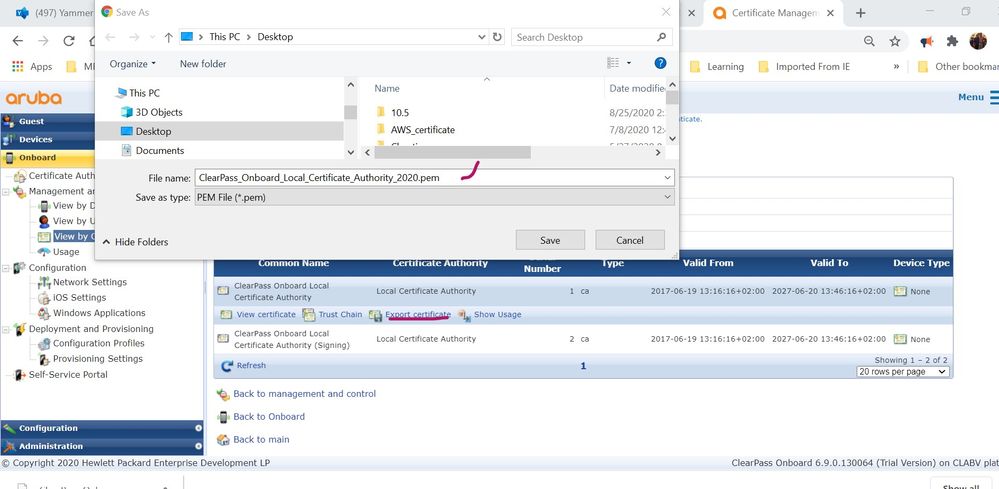
Step3: Click on Certificate Authorities, just follow below clicks to download clearpass certificate.
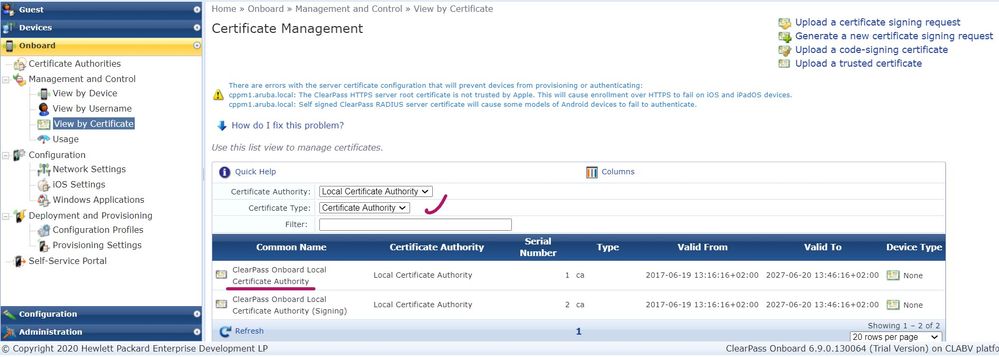
Once you the certificate you can install on AOS-CX switches as below:
6300-1-VSF# conf t6300-1-VSF(config)# crypto pki ta-profile DUR_clearpass6300-1-VSF(config-ta-DUR_clearpass)# end End current mode and change to enable mode. exit Exit current mode and change to previous mode list Print command list no Negate a command or set its defaults ocsp Configure Online Certificate Status Protocol revocation-check Configure revocation checking. (Default: no checking) show Show running system information ta-certificate Import a TA certificate in PEM format (Default: terminal)6300-1-VSF(config-ta-DUR_clearpass)# ta-certificatePaste the certificate in PEM format below, then hit enter and ctrl-D:6300-1-VSF(config-ta-cert)#-----BEGIN CERTIFICATE-----MIIEgzCCA2ugAwIBAgIBATANBgkqhkiG9w0BAQ0FADCByDELMAkGA1UEBhMCVVMxEzARBgNVBAgMCkNhbGlmb3JuaWExEjAQBgNVBAcMCVN1bm55dmFsZTEXMBUGA1UECgwOQXJ1YmEgTmV0d29ya3MxNjA0BgNVBAMMLUNsZWFyUGFzcyBPbmJvYXJkIExvY2FsIENlcnRpZmljYXRlIEF1dGhvcml0eTE/MD0GCSqGSIb3DQEJARYwZTMzZGNhOTgtM2RjNC00YWQ1LTgyYmMtZjE2NGEyYWQ5MjhhQGV4YW1wbGUuY29tMB4XDTE3MDYxOTExMTYxNloXDTI3MDYyMDExNDYxNlowgcgxCzAJBgNVBAYTAlVTMRMwEQYDVQQIDApDYWxpZm9ybmlhMRIwEAYDVQQHDAlTdW5ueXZhbGUxFzAVBgNVBAoMDkFydWJhIE5ldHdvcmtzMTYwNAYDVQQDDC1DbGVhclBhc3MgT25ib2FyZCBMb2NhbCBDZXJ0aWZpY2F0ZSBBdXRob3JpdHkxPzA9BgkqhkiG9w0BCQEWMGUzM2RjYTk4LTNkYzQtNGFkNS04MmJjLWYxNjRhMmFkOTI4YUBleGFtcGxlLmNvbTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBALqsCtNmOtiRGJ5iTYYr/tbVLK5tBCvJ0bCHn0pAvzcRwyvh75Cgr5XG+5J6MoWMZIyBMQC9nbyf5N6ugKkvSrqiujBLUizerEJt0D0E9U/9+X8kDeTM5LFDwHHlav0dxHPyoSM6eAvYI2Bcp1Qgj0ZJRQ7A9EyyaIprlGMK2YLXqF+C6A60diMm46bkv/qja1Y+0j7yvBF5c1iBYFI00QpIbpFKEn7T1cUW41d5TjkmctRIsDZzd3iHLZJK8MA/vDWTqs6n1WJBVs9VEXv4vagVrArWftx4JWsztCYyPRW1EvCtZkl+kT7a21BhX4f/HHjXNyWVlsmLNnjt1GOkc+MCAwEAAaN2MHQwHQYDVR0OBBYEFIEmd8oioP2boMGEupxfFvvcKn9OMA8GA1UdDwEB/wQFAwMHhgAwDwYDVR0TAQH/BAUwAwEB/zAxBgNVHSUEKjAoBggrBgEFBQcDCQYIKwYBBQUHAwIGCCsGAQUFBwMBBggrBgEFBQcDAzANBgkqhkiG9w0BAQ0FAAOCAQEAm+tPlFDDScOE9cmUN1r7GQNx3fD6g0zb33Si3ik/buAHcHmejtAzkjjLXpwUHMPzUmRsQMM0ZnOZCFfTgaHKeiQDQZn1lTOVFiFBe0aCmimRCUljeUTRSESEN5LLP1Y11hrFk1JIHwzZnmPS8Do50N9c/3KWFJW46dpmIyebSPgVqGiOJDLBVKOhNtY5O7F7IdJnAhlDEn5EwdAHgRNx/TXAIAR+V41uq744YiWQF+A1tpQD4RUuNWYADTHYvwvXCIugiQRqwmYjPMq6IL8325kZzE4X0bLf96/YQqdYsgACXcfOG8Oqx1hTg2QBQMQKKOwVoVCXwzf9UpEnl3Uugg==-----END CERTIFICATE-----6300-1-VSF(config-ta-cert)# -----> Press Ctrl+D
AOS-CX switch is ready for DUR.
Also you can find simple steps to configure DUR, LUR and more on below links:
Regards,
Yash