MSCHAPv2 should work with either ClearText and NT Hash. The field that you refer to in the LDAP, does it actually return the ClearText password with the BindDN that you configured? LDAP servers are typically configured to make it hard to get to the plaintext password, and by default not even store the password in plaintext as you really don't want your LDAP to be compromised and get all your plaintext password leaked.
You can use an LDAP Browser tool to connect with the same credentials and see if the password is indeed returned. If you use port 389 with plain LDAP, you can also run a packet capture and see if the password is in there, and if you see... that is the reason why you should not do this.
Also, while it works, try to get rid of EAP-PEAP MSCHAPv2 as MSCHAPv2 has been compromised as a security protocol and should not be used anymore. If you don't have 100% control over your endpoints (clients), and/or can't enforce the configuration for the SSID to validate the server certificate, like with Active Directory or an MDM tool, you put your users' credentials at risk. Move to EAP-TLS to be more secure.
If you still want to proceed with this... it may be good to work with Aruba Support to troubleshoot what is happening.
------------------------------
Herman Robers
------------------------
If you have urgent issues, always contact your Aruba partner, distributor, or Aruba TAC Support. Check
https://www.arubanetworks.com/support-services/contact-support/ for how to contact Aruba TAC. Any opinions expressed here are solely my own and not necessarily that of Hewlett Packard Enterprise or Aruba Networks.
In case your problem is solved, please invest the time to post a follow-up with the information on how you solved it. Others can benefit from that.
------------------------------
Original Message:
Sent: Sep 23, 2021 06:13 AM
From: Aria Adhiguna
Subject: Clearpass with Generic LDAP Failed
Hi, i have used the same configuration in clearpass, also with ClearText. I have also added eap-peap to the authentication method and removed eap-mschapv2, but for unknown reason it still doesn't work
------------------------------
Aria Adhiguna
Original Message:
Sent: Sep 22, 2021 03:47 PM
From: Sandeep Yadav
Subject: Clearpass with Generic LDAP Failed
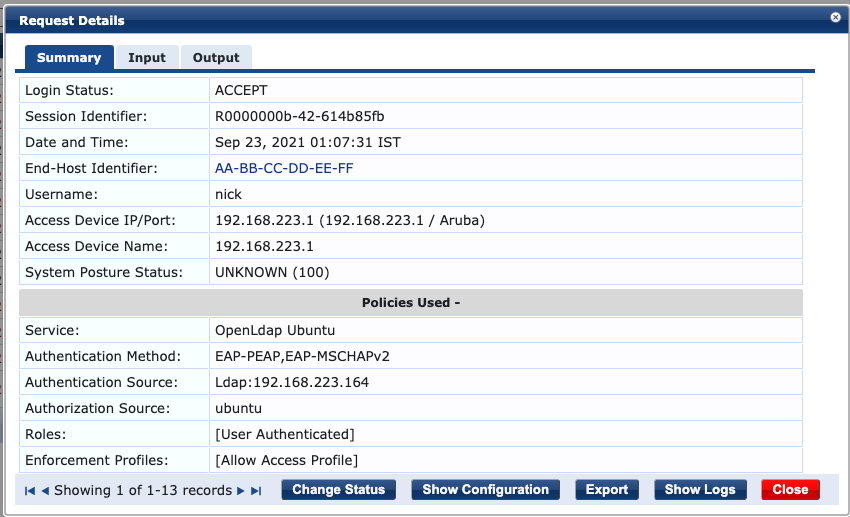
I have tested OpenLDAP on Ubuntu 20.04.1 LTS while using Generic LDAP Authentication Source for EAP-PEAP and it should work as long as the password is stored in ClearText
Below is the snippet of the source config:
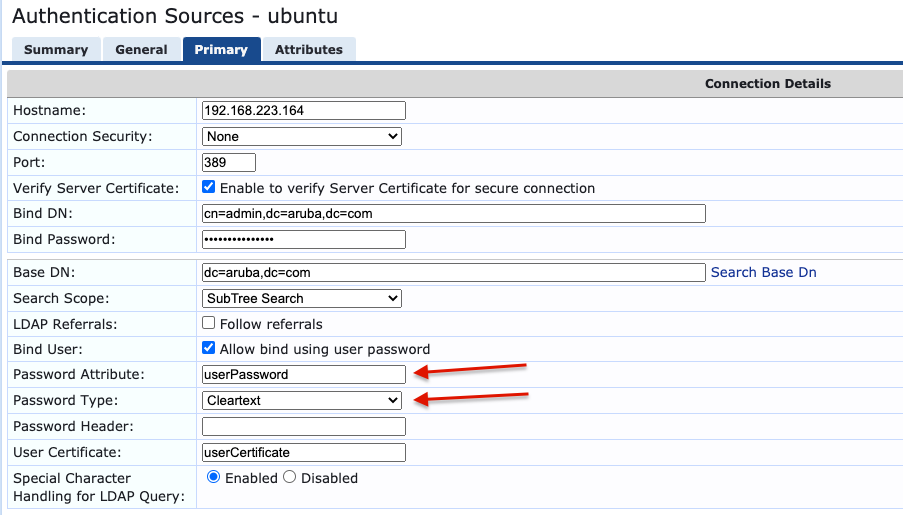
Account Password on OpenLDAP has to cleartext

------------------------------
SANDEEP YADAV
Global Escalation Center, ACCP
Original Message:
Sent: Sep 22, 2021 11:52 AM
From: Aria Adhiguna
Subject: Clearpass with Generic LDAP Failed
Im not sure what the LDAP directory is, but the customer said its ubuntu based
------------------------------
Aria Adhiguna
Original Message:
Sent: Sep 22, 2021 11:29 AM
From: Unknown User
Subject: Clearpass with Generic LDAP Failed
MS-CHAP2 is only possible with AD. If you are using something else as LDAP IdP then you should use EAP-GTC to authenticate users.
What LDAP directory are you using?
Original Message:
Sent: Sep 22, 2021 06:17 AM
From: Aria Adhiguna
Subject: Clearpass with Generic LDAP Failed
Hello,
We are doing a POC at a customer with LDAP. We first configured it to use local user and it worked, when we changed it to LDAP, it failed, here is the error message:


What should i check for this?
Thank you.
------------------------------
Aria Adhiguna
------------------------------