Original Message:
Sent: Oct 23, 2023 10:01 AM
From: Herman Robers
Subject: Setting up MPSK for headless/IoT devices
That is incorrect information, for example you can deploy Cisco iPSK with ClearPass as well (different name but similar feature as MPSK).
More important is if your WiFi solution supports MPSK, then how you supply the MPSK per client to your WiFI solution. If that is over (standardized) RADIUS attributes, there may be a good chance that ClearPass can send it.
A quick search suggests that people have been asking for MPSK on Unify, but it's not possible.
------------------------------
Herman Robers
------------------------
If you have urgent issues, always contact your Aruba partner, distributor, or Aruba TAC Support. Check https://www.arubanetworks.com/support-services/contact-support/ for how to contact Aruba TAC. Any opinions expressed here are solely my own and not necessarily that of Hewlett Packard Enterprise or Aruba Networks.
In case your problem is solved, please invest the time to post a follow-up with the information on how you solved it. Others can benefit from that.
Original Message:
Sent: Oct 20, 2023 03:47 PM
From: Miguel de Paula
Subject: Setting up MPSK for headless/IoT devices
Hey guys, okay?
From what I'm researching, it's only possible to use MPSK 100% with Aruba, right?
Why do I have a UNIFI controller solution and Clearpass, but I can't make it work?
And until then, all the information I found is from the Aruba controller, sometimes without Clearpass, but always with the Aruba controller.
Does anyone know if I can use another manufacturer integrated with Clearpass?
Original Message:
Sent: Apr 01, 2019 12:20 AM
From: Kapildev Erampu
Subject: Setting up MPSK for headless/IoT devices
Use Case:
The following is the use case addressed in this post.
The users access the Device Registration page using their Active Directory credentials and registers their headless/IoT devices.
The Multi Pre-Shared Key is sent via email to the user.
The user then connects his headless/IoT devices using the MPSK provided.
Requirements:
ArubaOS 8.4.0.0+
Clearpass 6.8+
How to Configure:
Create a new Operator Profile:
Create a new operator profile "Student" with access for managing devices on a network. Also select the user roles against which they can register their devices.
Clearpass Guest -> Administration -> Operator Logins -> Profiles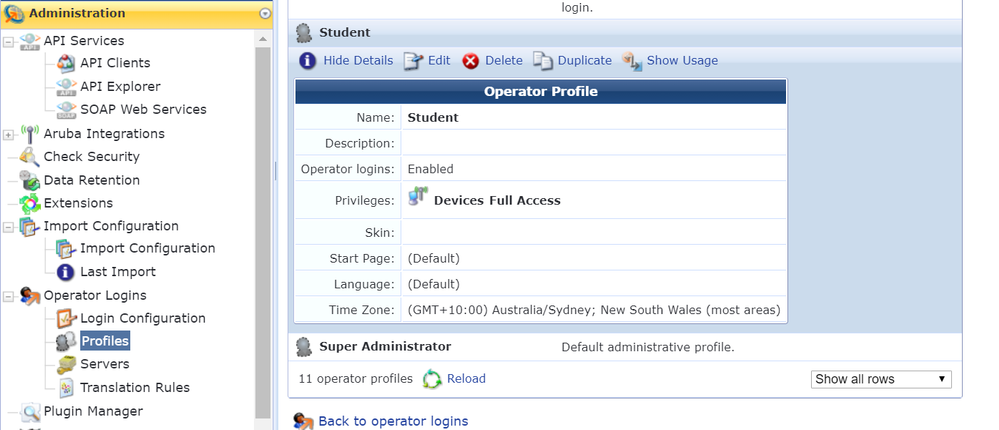
Create service to handle the user's access to the Device Registration page using the Active Directory credentials:
Enforcement policy controlling access to Device Registration page will return "admin_privileges = Student"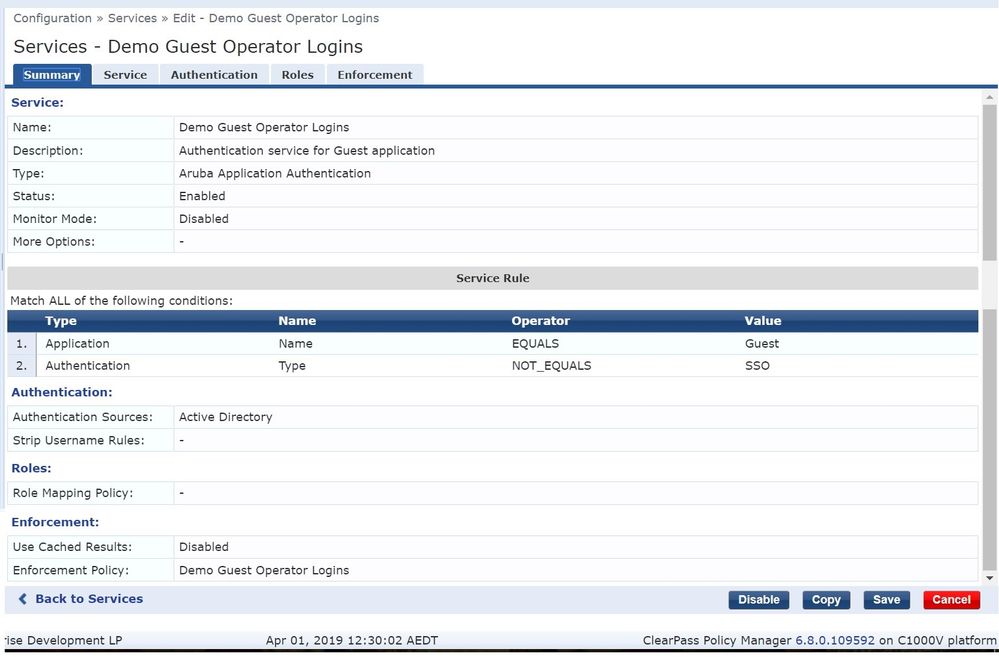
Create service to authenticate devices using an Aruba MPSK:
To configure MPSK on Clearpass use the service template "Aruba Wireless with MPSK"
Configuration -> Service Templates & Wizards -> Aruba Wireless with MPSK
Enter the prefix, Wireless device details, device roles (Tags) and finally map the tags to actual Aruba user-role. Please refer the screenshots below.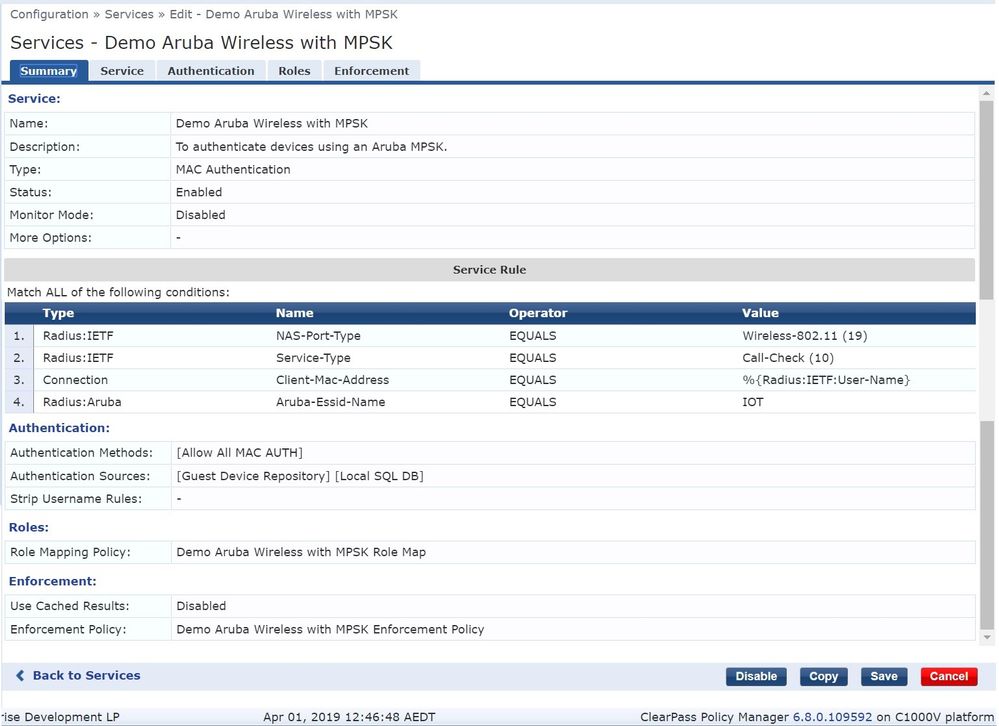
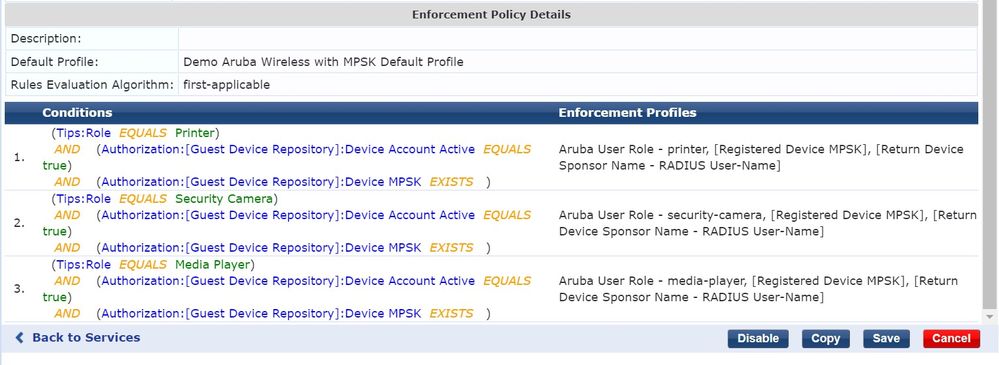
The following are returned as a part of the enforcement profile.
- Aruba user-role,
- Device's assigned MPSK that was generated automatically during Device Registration
- Guest Device repository sponsor name (In this case will be the AD username)
Make the Device Registration Page forms, MPSK aware:
Clearpass Guest -> Administration -> Aruba Integrations -> MPSK Configuration
In 'Deployment Mode', select the Radio button 'Always generate unique device WiFi passwords' and save configuration.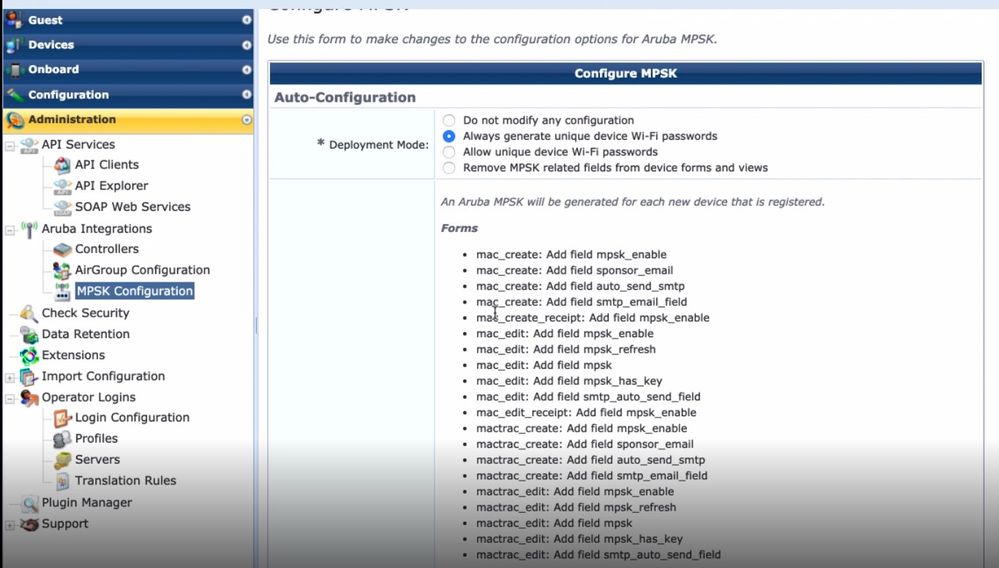
Setup the SMTP Server:
This will enable the MPSK receipt to be sent to the user, who is registering his device.
Configure SMTP server at Clearpass -> Administration -> External Servers -> Messaging Setup.
For more details refer the below post.
https://community.arubanetworks.com/t5/Education-Australia-New-Zealand/Sending-Emails-from-ClearPass-with-Gmail/gpm-p/427050
Controller Configuration:
Just use the Wizard
Managed Networks -> Select the hierarchy you want -> Configuration -> WLAN -> +
In the 'Security tab', Select WPA2-Personal -> 'Use Aruba MPSK' and associate Clearpass Server to it.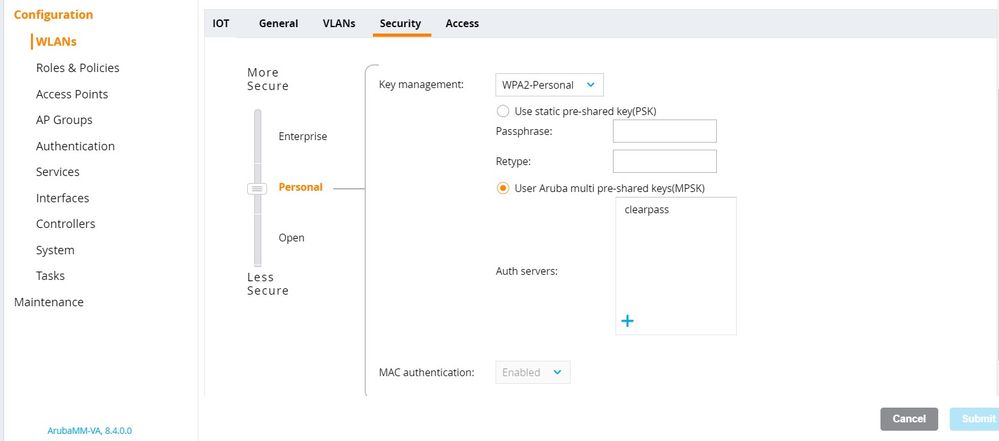
Create the user roles that are returned to controller under
Configuration -> Roles and Policies -> Roles -> +
Ensure the following parameters of AAA profile have the right server group associated.
- MAC Authentication Server Group
- RADIUS Accounting Server Group
- RFC 3576 Server
Demo:
Access the Device Registration Page and login using your AD credentials.
https://clearpass.arubatechs.com/guest/auth_login.php
Once you logged in, register your device by clicking on "Create Device"
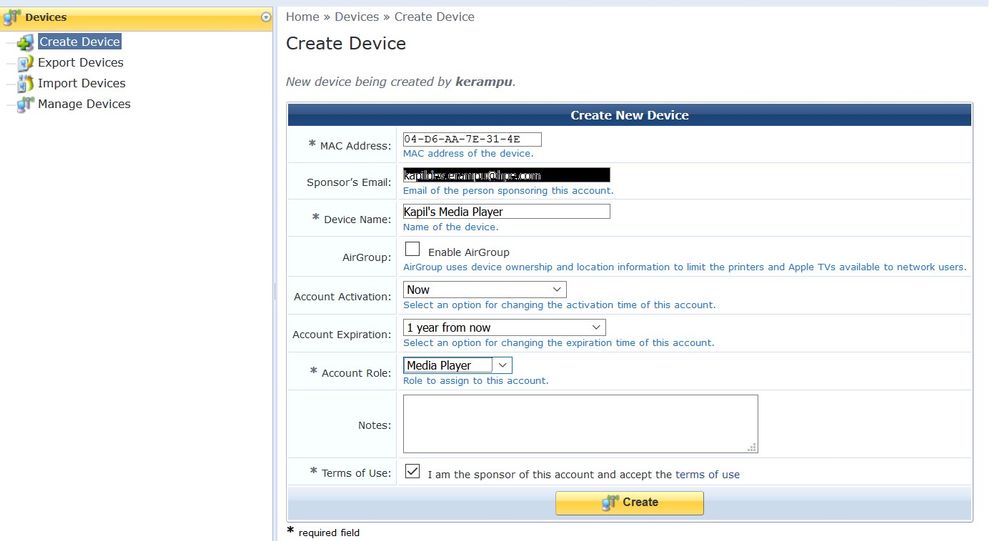
You will receive an email.
Now connect your media player to the SSID "IOT" using the MPSK provided in the email.
Controller Dashboard:
The media player is associated under the AD username 'kerampu'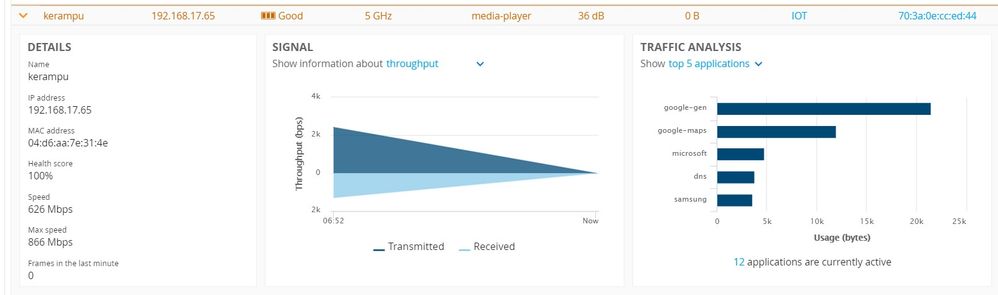
Clearpass Access Tracker: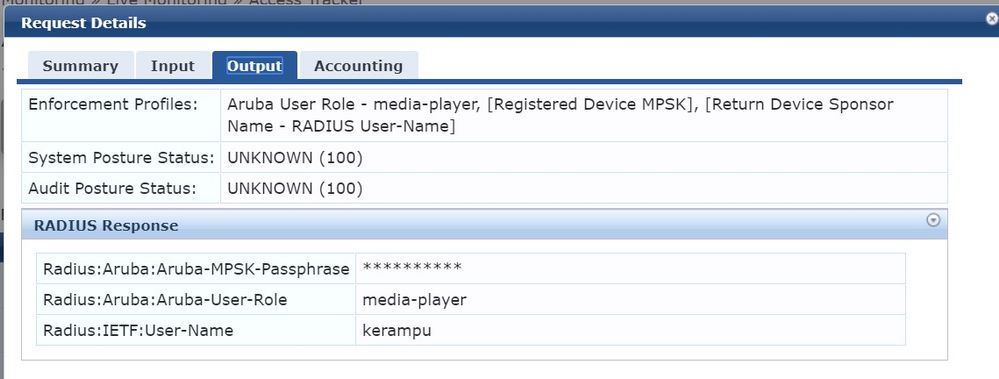
Hope you find this post useful. Please share your feedback.