I finally seem to have this working properly and here is how it went down:
I ended up creating three VLANs for specific ClearPass roles (the numbers have been changed to protect the innocent)
- VLAN 100 for Admin/Staff users AKA Admin role
- VLAN 200 for machine authentication (i.e. school owned laptops and wireless desktops sit idle on this VLAN when no one is logged into the machine) AKA Machine Auth role
- VLAN 300 for student users AKA Student role
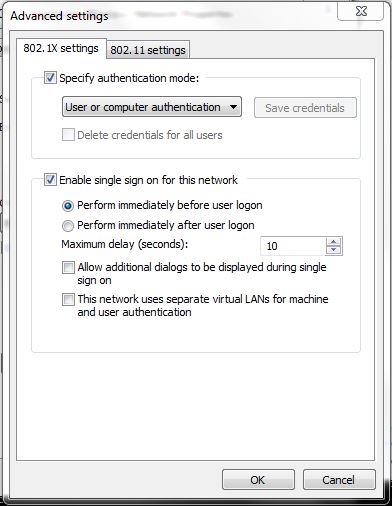
I dropped the DHCP lease time on VLAN 200 down to the AD minimum of 60 seconds based on some of the replies and other posts that I have read. Even at this point I was still having problems. Some students could login fine, others couldn't, some admin users could login fine and others couldn't. It was very strange. So I spent some time talking with our server team, the AD guys in particular and discovered that apparently some user accounts process faster than others. I am not an AD guy so I had no clue about this. This was the big revelation that sent me down the right path. I went back and took a look at our dot1x settings on the clients:
So after looking at this a little farther I had a hunch that since I had ClearPass authenticating first and THEN AD would authenticate the user on the box that it was a timing issue. So some accounts would take longer to process via ClearPass to get their role, so it would still be processing when the user box would try its AD authentication and since it was still in transition getting its role and VLAN and new IP, it couldn't find the AD server to authenticate the user to the box. You guys following me so far? I get fairly confused myself sometimes LOL.
That being said, I reversed the settings so it would allow the machines to authenticate via AD first then let ClearPass do its thing and set the roles. By default, there is a few seconds delay between authentication pieces so no more stepping on one another!:
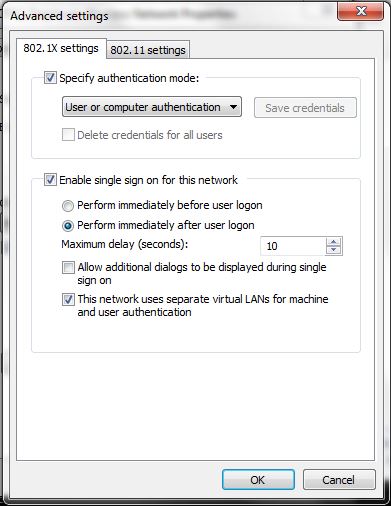
This reversal step seems to have cleared up almost all of my login authentication issues. The few issues that remain tend to be ID 10 T errors...