Hi,
i currently try to implement a session ACL that actively sends a reject to a TCP-Connection instead of just dropping the traffic so that the user's trying to access this service out of a wrong network have long timeouts and get a reject instantly.
And i didn't get it working. So i implemented a test-acl in my lab looking:
ip access-list session my-test-acl
any user svc-icmp permit
any any svc-icmp permit
any any svc-https deny send-deny-response
!
To reject all traffic to port 443. A web browser shows the same behaviour (it takes a very long time until a error is shown up) than the other app. So i started wireshark to examine it a bit and wireshark shows this:
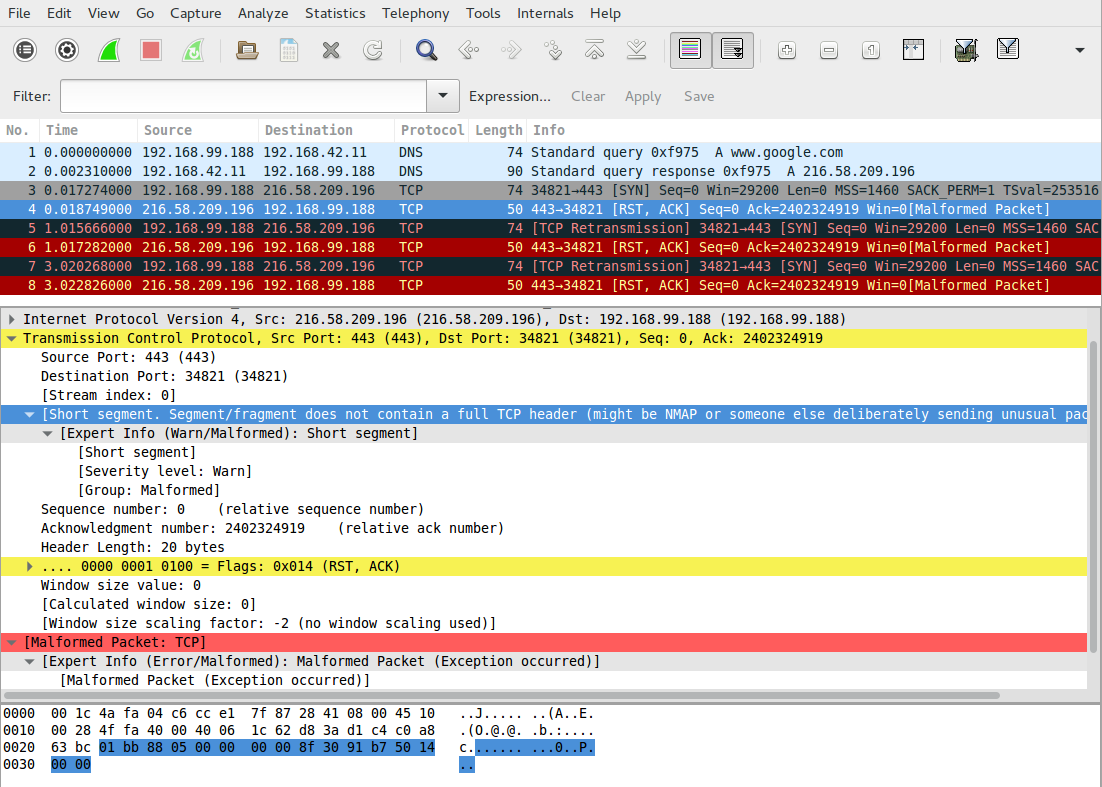
Initially i expected some ICMP packet to be sent from the aruba controller stating that the services is not reachable, but instead it seems that the controller answers with a TCP RST packet - but this packet seems to be malformed and so the client just drops it instead of processing it.
Did i miss something or is this the wrong way to 'reject' a TCP connection? Tried this with 6.4.3.4 and 6.4.4.1.
Thanks & Bye,
Chris