Virtual Routing and Forwarding:
Virtual Routing and Forwarding (VRF) is a Layer 3 level isolation to achieve Virtual Private Network (VPN).
Virtual routing and forwarding (VRF) is a technology that allows multiple instances of a routing table to co-exist within the same router.
Because the routing instances are independent, the same or overlapping IP addresses can be used without conflicting with each other.
Network functionality is improved because network paths can be segmented without requiring multiple routers.
Network Diagram:
ABBREVIATION:
HB: Heartbeat Link
VSX: Virtual Switching Extension
MC-LAG: Multi-chassis LAG
VRF: Virtual Routing and Forwarding
Checklist for configuring VRF on AOS-CX Switch:
It about using the command “vrf attach” to the L3 Interface.
We got two VRF here.,
Default: 172.30.29.0/24 TRANSIT SUBNET: 10.10.101.2
DOE: 10.10.200.0/24 TRANSIT SUBNET: 10.10.102.2
The transit subnet should also be a part of the VRF.
Since we only got one link from AOS-CX to 7005 Gateway, the links needs to be configured as trunk with multiple VLAN L3 interface, one for each VRF.
Create the VRF:
vrf DOE
Create the VLANs:
vlan 102
name DOE_Transit_Subnet
vlan 200
name DOE-Network
Define the connection mode and VLAN tagging:
interface lag 1 multi-chassis //Connection between 2930M and AOS-CX
vsx-sync vlans
no shutdown
description MC-LAG
no routing
vlan trunk native 101
vlan trunk allowed all
lacp mode active
interface 1/1/32
no shutdown
description From_2930M_Distribution_MCLAG
lag 1
interface 1/1/48 //Connection between the AOS-CX and the 7005 G/W
no shutdown
description To_7005_Gateway
no routing
vlan trunk native 101
vlan trunk allowed all
Doing the VRF Attach:
interface vlan102
vsx-sync active-gateways
vrf attach DOE
description DOE-Network
ip address 10.10.102.12/24
active-gateway ip mac 00:00:00:00:02:00
active-gateway ip 10.10.102.2
interface vlan200
vsx-sync active-gateways
vrf attach DOE
description DOE-Network
ip address 10.10.200.2/24
active-gateway ip mac 00:00:00:00:02:00
active-gateway ip 10.10.200.1
Remember to configure default Gateway on AOS-CX for each VRF:
ip route 0.0.0.0/0 10.10.102.1 vrf DOE //For VRF “DOE”
ip route 0.0.0.0/0 10.10.101.1 //For VRF “Default”
Also add the reverse route on the 7005 Gateway:
ip route 10.10.200.0 255.255.255.0 10.10.102.2 //For VRF “DOE”
ip route 172.30.29.0 255.255.255.0 10.10.101.2 //For VRF “Default”
In order to know how to configure VSX and MC-LAG, please refer the below link
https://community.arubanetworks.com/t5/Wired-Intelligent-Edge-Campus/ArubaOS-CX-Switches-VSX-and-MC-LAG/m-p/617685#M7734
VERIFICATION:
show vrf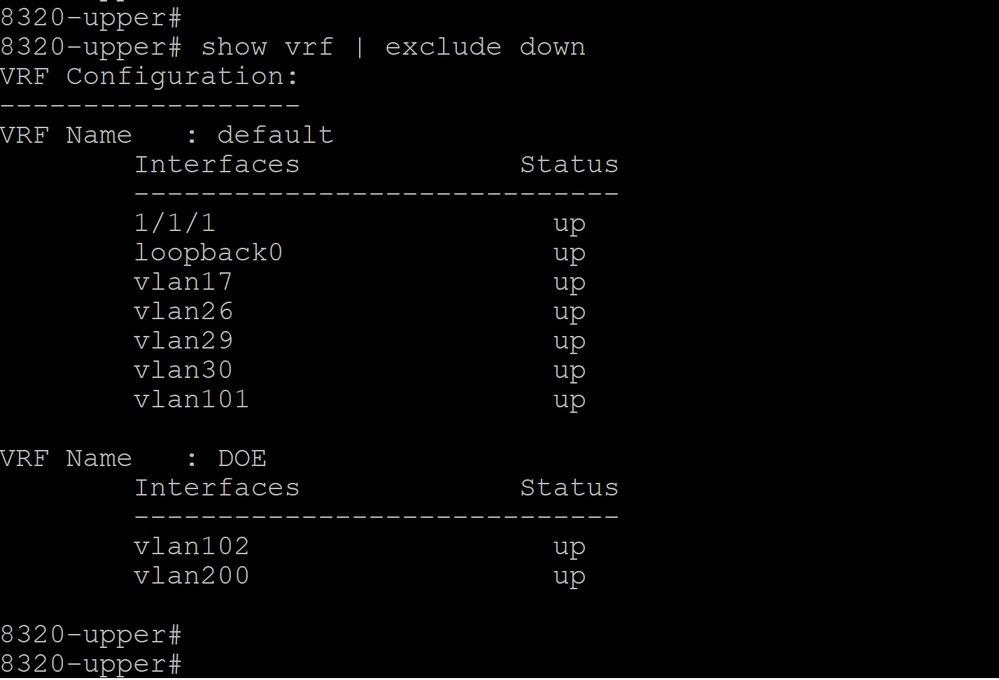
IP Inteface on Different VRF - show ip interface brief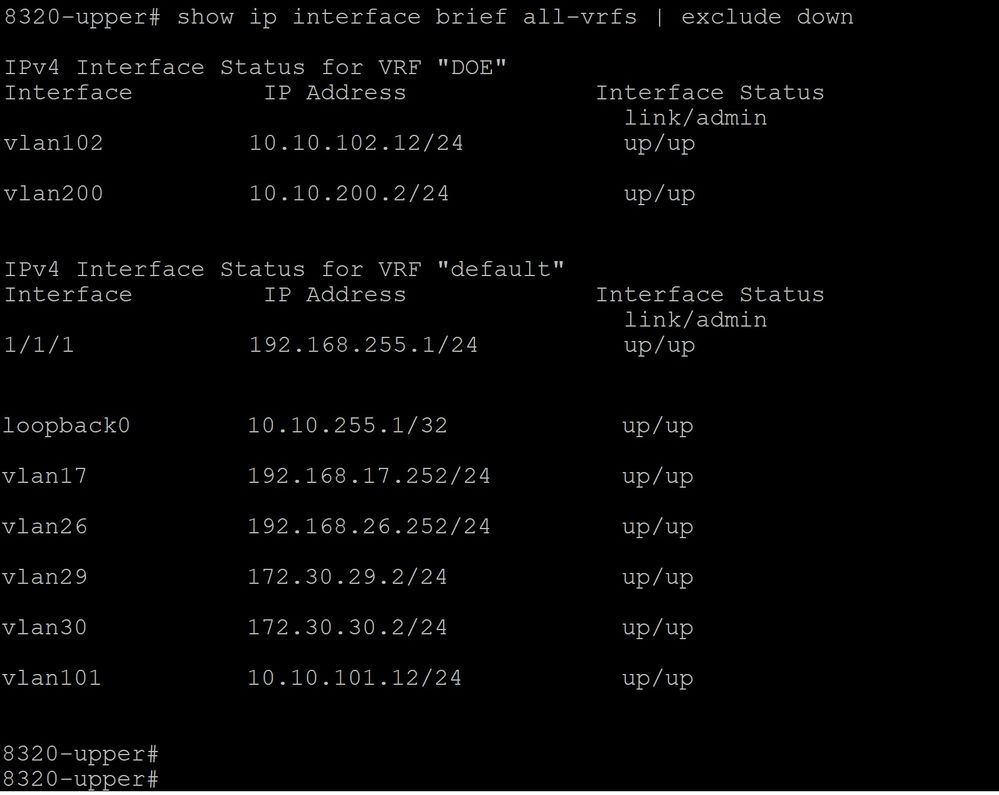
Routing Table: show ip route
Default VRF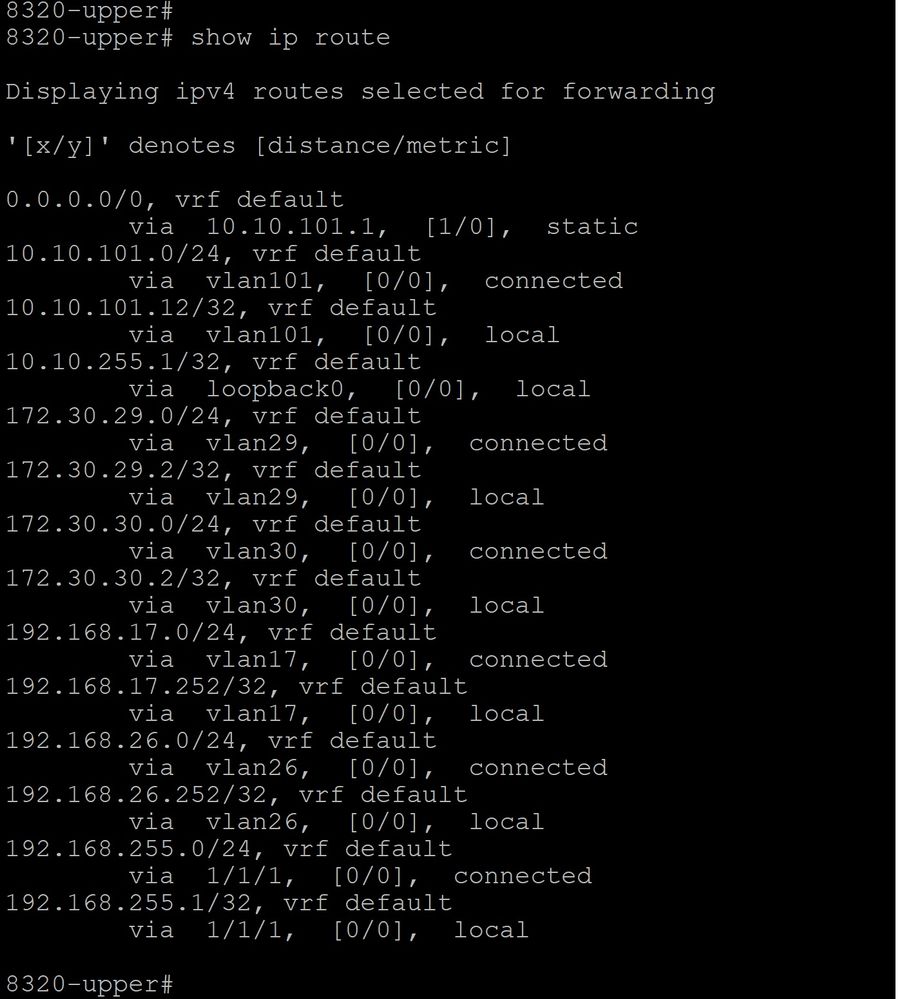
"DOE" VRF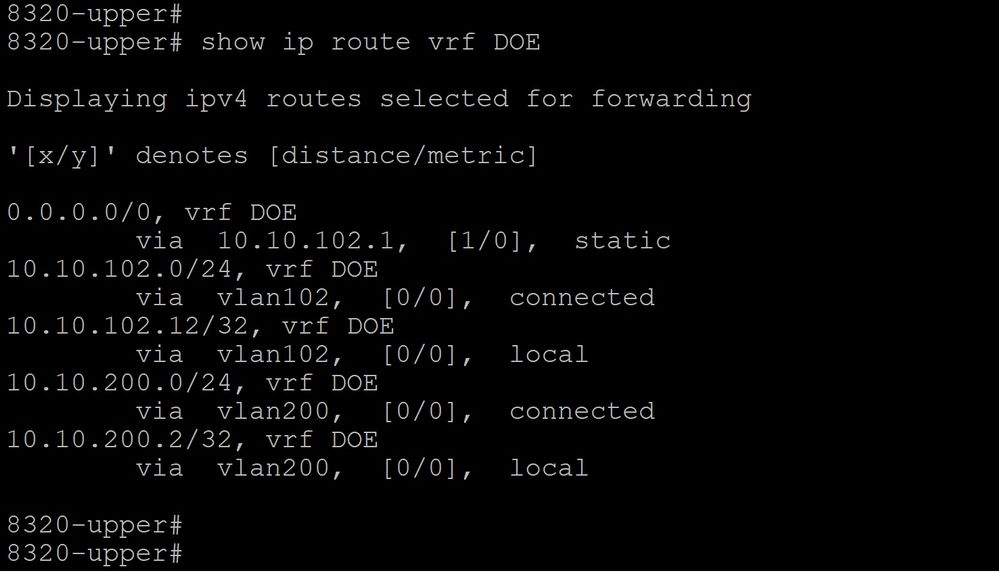
Checking the clients Pingability: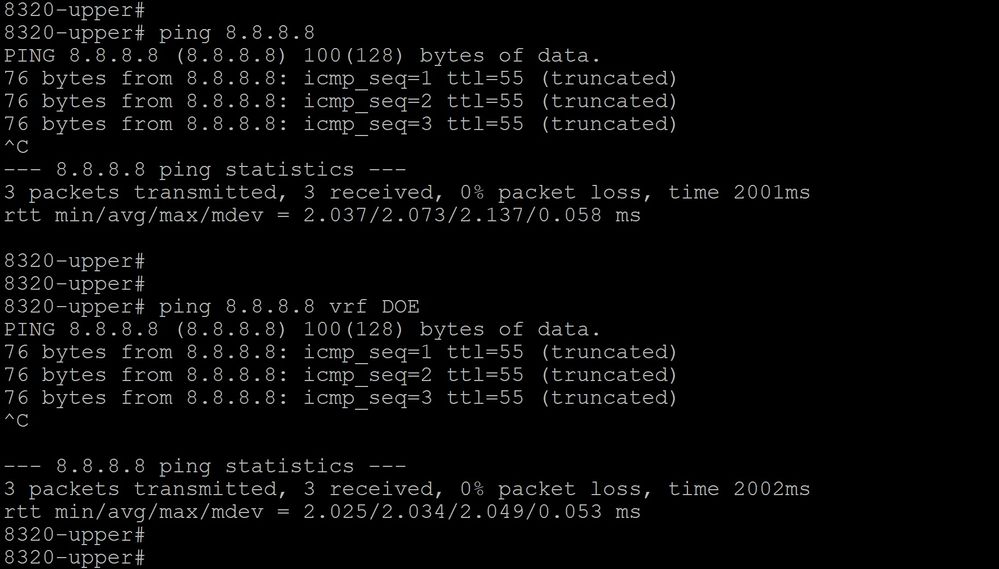
Hope you find this post useful !
#8320