OK. Well, to start in the Controller UI, take a look at Access Control under the Configuration tab. In order to write out a role for these phones, I would need to know what traffic they need to run other than SIP. Here is a brief sumary of my thoughts on this.
In our system, a role is a "stack" of policies. In the policies, there are the actual rules (permits/denies/QoS/etc). So, starting from the top down, here is how I would tackle this.
Controller based
First, proceed with defining your detination aliases. This is done to minimize the rules in the policies but to also make things more modular in the future. By using aliases, you can edit them, add to them, delete entries without having to re-write the policy. It's very handy.
1. Alias for SIP servers
2. Alias for DNS servers
3. Alias for internal networks (usually RFC 1918 addresses)
This is how that would look in the CLI
netdestination SIP-Servers
host 192.168.1.10
host 192.168.1.11
netdestination DNS-Servers
host 192.168.1.15
host 192.168.1.16
netdestination internal-nets
network 10.0.0.0 255.0.0.0
network 192.168.0.0 255.255.0.0
network 172.16.0.0 255.240.0.0
Second, define the Control traffic needed to get the phone up and operational such as
1. allow dhcp
2. allow bootp
3. allow ICMP
4. allow DNS to DNS servers
5. Deny things like DHCP server port and certain subnets
That would look like this in the CLI
ip access-list session logon-control
user any udp 68 deny
any any svc-icmp permit
any alias DNS-Servers svc-dns permit
any any svc-dhcp permit
any network 169.254.0.0 255.255.0.0 any deny
any network 240.0.0.0 240.0.0.0 any deny
Third, Define the SIP-VoIP policy and place in the high queue
This is a short example as there may be other protocols needed here.
ip access-list session sip-acl
any alias SIP-Servers svc-sip-udp permit queue high
any alias SIP-Servers svc-sip-tcp permit queue high
Last, create the role for voice
user-role voice
access-list session logon-control
access-list session sip-acl
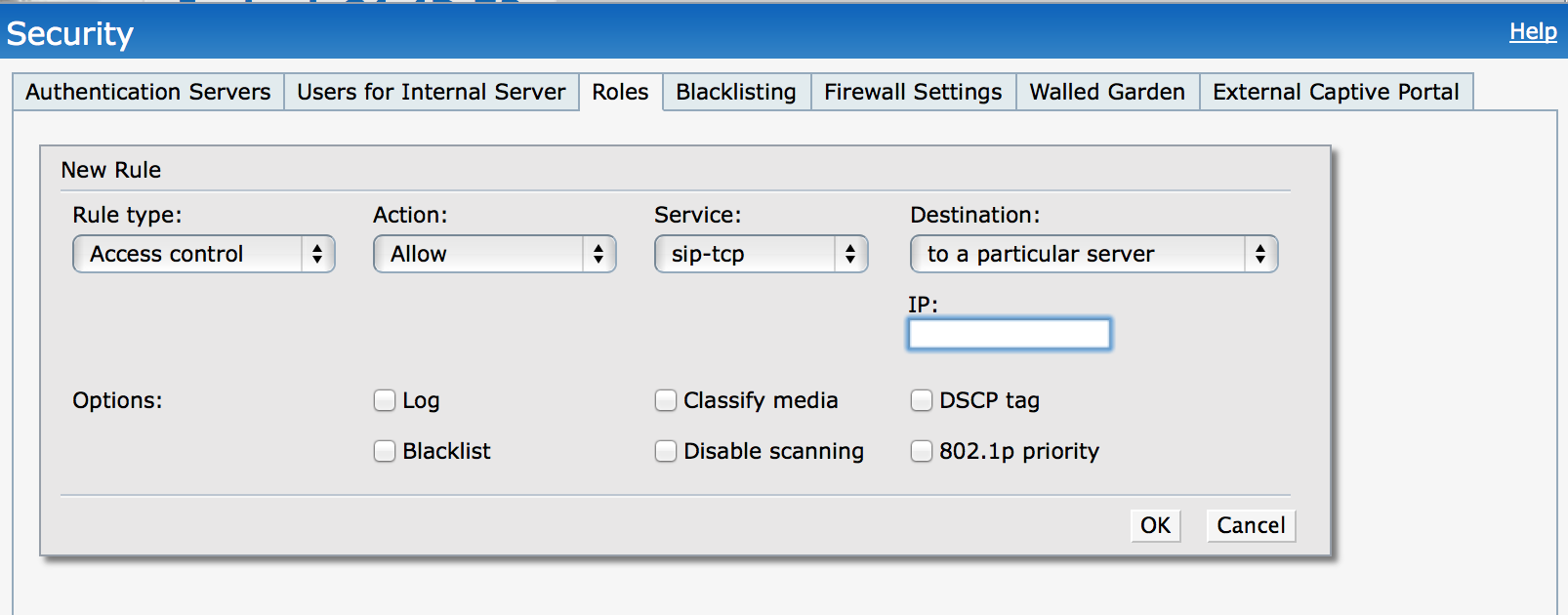
Instant (IAP) Based
Same theories apply but the implementation is a bit different. All policies are written under the role name. There is no concept of "stacking" firewall policies like the controller has. There is also no concept of creating aliases.
So, under the role, you will have a complete list of rules with the appropriate IP addresses or subnets for destinations. The thing to keep in mind is that you will need to select the appropriate priority for the packets based on the rules you are writing if they are unmarked (DSCP, 802.1p values). Also, for all VoIP traffic, tick off "Classify Media" to ensure it goes into the right queue.