Certain wireless deployments such as VoWiFi are very sensitive to loss of connectivity while client roams between APs. 802.11r / Fast BSS Transition (FT) is the IEEE amendment which focuses on reducing the time period for which client loses connectivity.
FT operates on below principles :
-
Authenticate client only when it initially enters the mobility domain (i.e. 802.11r mobility domain) by connecting to an AP
-
Do only key exchange when client roams to a new AP
-
The key exchange to new AP can happen
-
Over-the-Air :: Overloading key information with 802.11 auth & reassociation management frames which is part of any client roam event.
-
Over-the-DS :: Communicating to new AP thru the connected AP via wired infrastructure.
As of ArubaOS 6.3; below are the limitations of 802.11r feature in ArubaOS :
-
Only Over-the-Air FT is supported
-
FT roaming is only supported betweens APs in same 802.11r mobility domain within same controller i.e. inter-controller roaming isn't supported
-
FT roaming isn't supported in split-tunnel forward mode
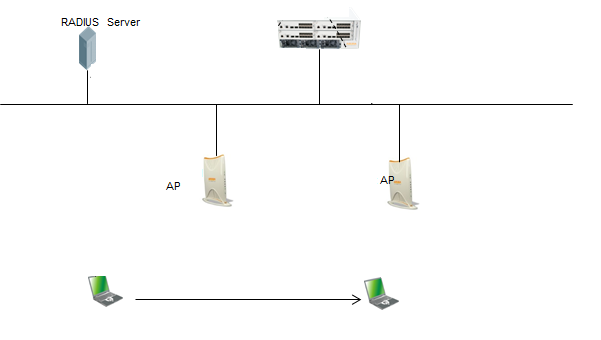
Environment: Any Aruba Campus or Remote AP deployment running ArubaOS 6.3.0.0 or above.
Network Topology: Any campus or remote AP deployment with roaming client.
Creation of 11r Profile ::
(Aruba-Master) (config) #wlan dot11r-profile voice
(Aruba-Master) (802.11r Profile "voice") #dot11r
(Aruba-Master) (802.11r Profile "voice") #exit
(Aruba-Master) (config) #show wlan dot11r-profile voice
Mapping to SSID Profile ::
(Aruba-Master) (config) #wlan ssid-profile voice dot11r-profile voice
(Aruba-Master) (config) #write memory
Configuration Validation ::
Aruba-Master) (config) #show wlan dot11r-profile voice
802.11r Profile "voice"
-----------------------
Parameter Value
--------- -----
Advertise 802.11r Capability Enabled
802.11r Mobility Domain ID 1
802.11r R1 Key Duration 3600
802.11r R1 Key Assignment dynamic
(Aruba-Master) (config) #show wlan ssid-profile voice
SSID Profile "voice"
-------------------
Parameter Value
--------- -----
SSID enable Enabled
ESSID voice
Encryption wpa2-aes
DTIM Interval 2 beacon periods
802.11a Basic Rates 12 18 24 36 48 54
802.11a Transmit Rates 12 18 24 36 48 54
802.11g Basic Rates 11 12 18 24 36 48 54
802.11g Transmit Rates 11 12 18 24 36 48 54
Station Ageout Time 1000 sec
Max Transmit Attempts 8
RTS Threshold 2333 bytes
Short Preamble Enabled
Max Associations 64
Wireless Multimedia (WMM) Enabled
Wireless Multimedia U-APSD (WMM-UAPSD) Powersave Enabled
WMM TSPEC Min Inactivity Interval 0 msec
Override DSCP mappings for WMM clients Disabled
DSCP mapping for WMM voice AC 46
DSCP mapping for WMM video AC N/A
DSCP mapping for WMM best-effort AC N/A
DSCP mapping for WMM background AC N/A
Multiple Tx Replay Counters Disabled
Hide SSID Disabled
Deny_Broadcast Probes Disabled
Local Probe Request Threshold (dB) 20
Disable Probe Retry Enabled
Battery Boost Disabled
WEP Key 1 N/A
WEP Key 2 N/A
WEP Key 3 N/A
WEP Key 4 N/A
WEP Transmit Key Index 1
WPA Hexkey N/A
WPA Passphrase ********
Maximum Transmit Failures 30
EDCA Parameters Station profile N/A
EDCA Parameters AP profile N/A
BC/MC Rate Optimization Enabled
Rate Optimization for delivering EAPOL frames Enabled
Strict Spectralink Voice Protocol (SVP) Disabled
High-throughput SSID Profile HT-On
802.11g Beacon Rate 12
802.11a Beacon Rate 18
Advertise QBSS Load IE Disabled
Advertise Location Info Disabled
Advertise AP Name Disabled
802.11r Profile voice
Enforce user vlan for open stations Disabled
Working Validation :
auth-tracebuf command can be used to validate that the client isn't doing complete 802.1x (or just key exchange as in OKC) while roaming between APs.
(Aruba-Local) # show auth-tracebuf mac 48:74:6e:d1:29:0f
Warning: user-debug is enabled on one or more specific MAC addresses;
only those MAC addresses appear in the trace buffer.
Auth Trace Buffer
-----------------
Jun 25 08:29:17 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 - - wpa2 aes
Jun 25 08:29:17 eap-id-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 1 5
Jun 25 08:29:17 eap-id-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 1 19 Voice_Pilot
Jun 25 08:29:17 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 193 219
Jun 25 08:29:17 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 193 90
Jun 25 08:29:17 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 2 6
Jun 25 08:29:17 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 2 152
Jun 25 08:29:17 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 202 390
Jun 25 08:29:17 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 202 1188 <-- Complete Authentication happen once
Jun 25 08:29:17 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 3 1096
Jun 25 08:29:17 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 3 6
Jun 25 08:29:17 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 115 244
Jun 25 08:29:17 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 115 1188
Jun 25 08:29:17 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 4 1096
Jun 25 08:29:17 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 4 6
Jun 25 08:29:17 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 97 244
Jun 25 08:29:17 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 97 712
Jun 25 08:29:17 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 5 624
Jun 25 08:29:19 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 5 348
Jun 25 08:29:19 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 237 588
Jun 25 08:29:19 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 237 153
Jun 25 08:29:19 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 6 69
Jun 25 08:29:19 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 6 6
Jun 25 08:29:19 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 249 244
Jun 25 08:29:19 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 249 127
Jun 25 08:29:19 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 7 43
Jun 25 08:29:19 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 7 59
Jun 25 08:29:19 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 137 297
Jun 25 08:29:19 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 137 143
Jun 25 08:29:19 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 8 59
Jun 25 08:29:19 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 8 59
Jun 25 08:29:19 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 211 297
Jun 25 08:29:19 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 211 159
Jun 25 08:29:19 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 9 75
Jun 25 08:29:19 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 9 107
Jun 25 08:29:19 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 73 345
Jun 25 08:29:19 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 73 175
Jun 25 08:29:19 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 10 91
Jun 25 08:29:19 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 10 43
Jun 25 08:29:19 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 86 281
Jun 25 08:29:19 rad-resp <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 86 191
Jun 25 08:29:19 eap-req <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 12 107
Jun 25 08:29:19 eap-resp -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 12 43
Jun 25 08:29:19 rad-req -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 199 281
Jun 25 08:29:19 rad-accept <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43/PTP-Radius 199 330
Jun 25 08:29:19 eap-success <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 12 4
Jun 25 08:29:19 wpa2-key1 <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 - 117
Jun 25 08:29:19 wpa2-key2 -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 - 240
Jun 25 08:29:19 wpa2-key3 <- 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 - 279
Jun 25 08:29:19 wpa2-key4 -> 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 - 95
Jun 25 08:30:13 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b3:49:43 - -
Jun 25 08:30:13 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:63 - - wpa2 aes
Jun 25 08:30:21 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:63 - -
Jun 25 08:30:21 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:ab:23 - - wpa2 aes
Jun 25 08:30:38 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:ab:23 - -
Jun 25 08:30:38 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b3:60:23 - - wpa2 aes
Jun 25 08:30:47 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b3:60:23 - -
Jun 25 08:30:47 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b3:4b:e3 - - wpa2 aes
Jun 25 08:30:55 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b3:4b:e3 - -
Jun 25 08:30:55 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:b0:03 - - wpa2 aes
Jun 25 08:31:08 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:b0:03 - -
Jun 25 08:31:08 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:43 - - wpa2 aes
Jun 25 08:31:30 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:43 - -
Jun 25 08:31:30 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b3:60:03 - - wpa2 aes
Jun 25 08:31:44 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b3:60:03 - -
Jun 25 08:31:44 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:af:03 - - wpa2 aes <-- 802.11r in action.
Jun 25 08:32:00 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:af:03 - -
Jun 25 08:32:00 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b3:60:03 - - wpa2 aes
Jun 25 08:32:16 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b3:60:03 - -
Jun 25 08:32:16 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:43 - - wpa2 aes
Jun 25 08:32:25 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:43 - -
Jun 25 08:32:25 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:8e:43 - - wpa2 aes
Jun 25 08:32:43 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:8e:43 - -
Jun 25 08:32:43 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:c3 - - wpa2 aes
Jun 25 08:32:52 station-down * 48:74:6e:d1:29:0f 9c:1c:12:b1:a6:c3 - -
Jun 25 08:32:52 station-up * 48:74:6e:d1:29:0f 9c:1c:12:b1:aa:c3 - - wpa2 aes
Validate whether AP has "r" flag i.e. SSID with 11r is mapped to right AP-Group.
show ap active
Active AP Table
---------------
Name Group IP Address 11g Clients 11g Ch/EIRP/MaxEIRP 11a Clients 11a Ch/EIRP/MaxEIRP AP Type Flags Uptime Outer IP
---- ----- ---------- ----------- ------------------- ----------- ------------------- ------- ----- ------ --------
1-3-1152A Test-AP-Group 192.168.99.203 1 AP:HT:1/12/21.5 0 AP:HT:48-/12/22 135 Aar 40d:11h:36m:41s N/A
1-4-1101A Test-AP-Group 192.168.98.86 2 AP:HT:1/12/21.5 0 AP:HT:48-/21.5/22 135 Aar 7d:17h:58m:13s N/A
1-3-1169A Test-AP-Group 192.168.98.14 3 AP:HT:1/12/21.5 0 AP:HT:48-/21.5/22 135 Aar 40d:11h:36m:56s N/A
1-3-1155A Test-AP-Group 192.168.99.106 3 AP:HT:1/12/21.5 0 AP:HT:157+/12/22.5 135 Aar 45d:21h:24m:43s N/A
1-3-1172A Test-AP-Group 192.168.98.175 2 AP:HT:1/12/21.5 1 AP:HT:149+/12/22.5 135 Aar 40d:11h:36m:53s N/A
1-5-1056A Test-AP-Group 192.168.98.107 1 AP:HT:11/12/21.5 0 AP:HT:157+/22.5/22.5 135 Aar 38d:21h:35m:47s N/A
1-3-1148A Test-AP-Group 192.168.99.109 0 AP:HT:11/12/21.5 1 AP:HT:44+/21.5/22 135 Aar 40d:11h:36m:34s N/A
Flags: 1 = 802.1x authenticated AP; 2 = Using IKE version 2;
A = Enet1 in active/standby mode; B = Battery Boost On; C = Cellular;
D = Disconn. Extra Calls On; E = Wired AP enabled; F = AP failed 802.1x authentication;
H = Hotspot Enabled; K = 802.11K Enabled; L = Client Balancing Enabled; M = Mesh;
N = 802.11b protection disabled; P = PPPOE; R = Remote AP;
S = AP connected as standby; X = Maintenance Mode;
a = Reduce ARP packets in the air; d = Drop Mcast/Bcast On; u = Custom-Cert RAP;
r = 802.11r Enabled
CAC Flags: H = Handover Resv. Threshold Reached; P = Peak Cap. Reached
Validate if the client is 11r capable.
show ap association
Association Table
-----------------
Name bssid mac auth assoc aid l-int essid vlan-id tunnel-id phy assoc. time num assoc Flags Band steer moves (T/S)
---- ----- --- ---- ----- --- ----- ----- ------- --------- --- ----------- --------- ----- ----------------------
CUP-3-1159A 9c:1c:12:b3:60:03 48:74:6e:dd:27:c8 y y 1 20 voice 2160 0x1028f g-HT-20-1ss 8m:18s 1 WRA 0/0
CUP-3-1159A 9c:1c:12:b3:60:03 00:88:65:72:3c:2c y y 2 20 voice 2160 0x1028f g-HT-20sgi-1ss 16s 2 WRAB 22/18
CUP-3-1163A 9c:1c:12:b1:a6:d3 94:94:26:95:5d:38 y y 1 20 voice 2160 0x105cc a-HT-40sgi-1ss 9m:1s 2 WRAB 3/3
CUP-3-1163A 9c:1c:12:b1:a6:c3 48:74:6e:d2:13:69 y y 2 20 voice 2160 0x109dc g-HT-20-1ss 1m:44s 1 WRA 0/0
The phy column shows client's operational capabilities for current association
Flags: A: Active, B: Band Steerable, H: Hotspot(802.11u) client, K: 802.11K client, R: 802.11R client, W: WMM client, w: 802.11w client
PHY Details: HT : High throughput; 20: 20MHz; 40: 40MHz
VHT : Very High throughput; 80: 80MHz; 160: 160MHz; 80p80: 80MHz + 80MHz
<n>ss: <n> spatial streams
Validate if client is sending MDIE & PMKID by enabling user-debug.
Jun 25 08:33:40 stm[3471]: <501095> <NOTI> |stm| Assoc request @ 08:33:40.166921: 48:74:6e:d0:56:9d (SN 2774): AP 192.168.99.77-9c:1c:12:b1:aa:c3-TestAP1
Jun 25 08:33:40 authmgr[3470]: <522036> <INFO> |authmgr| MAC=48:74:6e:d0:56:9d Station DN: BSSID=9c:1c:12:b1:a6:c3 ESSID=voice VLAN=2160 AP-name=CUP-3-1163A
Jun 25 08:33:40 authmgr[3470]: <522234> <DBUG> |authmgr| Setting idle timer for user 48:74:6e:d0:56:9d to 300 seconds (idle timeout: 300 ageout: 0).
Jun 25 08:33:40 authmgr[3470]: <522152> <DBUG> |authmgr| station free: bssid=9c:1c:12:b1:a6:c3, @=0x0x11345cc.
Jun 25 08:33:40 stm[3471]: <501080> <NOTI> |stm| Deauth to sta: 48:74:6e:d0:56:9d: Ageout AP 192.168.98.167-9c:1c:12:b1:a6:c3-CUP-3-1163A STA has roamed to another AP
Jun 25 08:33:40 stm[3471]: <501100> <NOTI> |stm| Assoc success @ 08:33:40.167728: 48:74:6e:d0:56:9d: AP 192.168.99.77-9c:1c:12:b1:aa:c3-TestAP1
Jun 25 08:33:40 authmgr[3470]: <522035> <INFO> |authmgr| MAC=48:74:6e:d0:56:9d Station UP: BSSID=9c:1c:12:b1:aa:c3 ESSID=voice VLAN=2160 AP-name=TestAP1
Jun 25 08:33:40 authmgr[3470]: <522077> <DBUG> |authmgr| MAC=48:74:6e:d0:56:9d ingress 0x0x10353 (tunnel 851), u_encr 64, m_encr 64, slotport 0x0x2100 , type: local, FW mode: 0, AP IP: 0.0.0.0 mdie 1 ft_complete 0
Jun 25 08:33:40 authmgr[3470]: <522078> <DBUG> |authmgr| MAC=48:74:6e:d0:56:9d, wired: 0, vlan:2160 ingress:0x0x10353 (tunnel 851), ingress:0x0x10353 new_aaa_prof: voice, stored profile: voice stored wired: 0 stored essid: voice, stored-ingress: 0x0x1053d
Jun 25 08:33:40 authmgr[3470]: <522247> <DBUG> |authmgr| User idle timer removed for user with MAC 48:74:6e:d0:56:9d.
Jun 25 08:33:40 authmgr[3470]: <522258> <DBUG> |authmgr| "VDR - Add to history of user user 48:74:6e:d0:56:9d vlan 0 derivation_type Reset VLANs for Station up index 15.
Jun 25 08:33:40 authmgr[3470]: <522255> <DBUG> |authmgr| "VDR - set vlan in user for 48:74:6e:d0:56:9d vlan 2160 fwdmode 0 derivation_type Default VLAN.
Jun 25 08:33:40 authmgr[3470]: <522258> <DBUG> |authmgr| "VDR - Add to history of user user 48:74:6e:d0:56:9d vlan 2160 derivation_type Default VLAN index 16.
Jun 25 08:33:40 authmgr[3470]: <522255> <DBUG> |authmgr| "VDR - set vlan in user for 48:74:6e:d0:56:9d vlan 2160 fwdmode 0 derivation_type Current VLAN updated.
Jun 25 08:33:40 authmgr[3470]: <522258> <DBUG> |authmgr| "VDR - Add to history of user user 48:74:6e:d0:56:9d vlan 2160 derivation_type Current VLAN updated index 17.
Jun 25 08:33:40 authmgr[3470]: <522246> <DBUG> |authmgr| Idle timeout should be driven by STM for MAC 48:74:6e:d0:56:9d.
Jun 25 08:33:40 authmgr[3470]: <522254> <DBUG> |authmgr| VDR - mac 48:74:6e:d0:56:9d rolename logon fwdmode 0 derivation_type Initial Role Contained vp not present.
Jun 25 08:33:40 authmgr[3470]: <522258> <DBUG> |authmgr| "VDR - Add to history of user user 48:74:6e:d0:56:9d vlan 0 derivation_type Reset Role Based VLANs index 18.
Jun 25 08:33:40 authmgr[3470]: <522083> <DBUG> |authmgr| Skip User-Derivation, mba:0 udr_exist:0,default_role:logon,pDefRole:0x0xeb1c44
Jun 25 08:33:40 authmgr[3470]: <524124> <DBUG> |authmgr| dot1x_supplicant_up(): MAC:48:74:6e:d0:56:9d, pmkid_present:True, pmkid:bf 11 bd c6 d8 11 0b aa 74 10 1d 71 0e 6d ad 48
Jun 25 08:33:40 authmgr[3470]: <522243> <DBUG> |authmgr| MAC=48:74:6e:d0:56:9d Station Updated Update MMS: BSSID=9c:1c:12:b1:aa:c3 ESSID=voice VLAN=2160 AP-name=TestAP1
Jun 25 08:33:40 authmgr[3470]: <522035> <INFO> |authmgr| MAC=48:74:6e:d0:56:9d Station UP: BSSID=9c:1c:12:b1:aa:c3 ESSID=voice VLAN=2160 AP-name=TestAP1
Jun 25 08:33:40 authmgr[3470]: <522077> <DBUG> |authmgr| MAC=48:74:6e:d0:56:9d ingress 0x0x10353 (tunnel 851), u_encr 64, m_encr 64, slotport 0x0x2100 , type: local, FW mode: 0, AP IP: 0.0.0.0 mdie 1 ft_complete 1
In addition to logging; Over The Air capture can be collected to validate client / AP packet transactions.
In case of Bridge / Decrypt-Tunnel; AP is the holder of R1 key. To validate if the AP has R1 key; below command can be used.
(Aruba3600) #show ap debug dot11r state ap-name TestAP
Stored R1 Keys
--------------
Station MAC Mobility Domain ID Validity Duration R1 Key
----------- ------------------ ----------------- ------
48:74:6e:d0:56:9d 1 3492 (32): 49 ae d2 8f 96 8f e8 ba 3d c6 f5 fa 15 ea a9 fd d3 82 5e 86 ab 09 34 2d 3d 62 3c b5 79 22 f5 af
To remove the key for a client; we can use the command
(Aruba3600) #ap debug dot11r remove-key 48:74:6e:d0:56:9d ap-name TestAP
(Aruba3600) #show ap debug dot11r state ap-name TestAP
Stored R1 Keys
--------------
Station MAC Mobility Domain ID Validity Duration R1 Key
----------- ------------------ ----------------- ------
The command "show ap debug dot11r efficiency" can be used to check hit / miss % of R1 key.
(UPHS-HUP-Local-PMC) #show ap debug dot11r efficiency
Fast Roaming R1 Key Efficiency
------------------------------
Client MAC Hit (%) Miss (%)
---------- ------- --------
48:74:6e:d0:56:9d 0 (0%) 0 (0%)