Since I couldn't find a way to see any ldap logs on the IAP, I started tcpdump on the ldapserver to see what happened, and then I managed to find out that the key attribute is acually cn, not like I was thinking this is the attribute for the password.
Here are my findings:
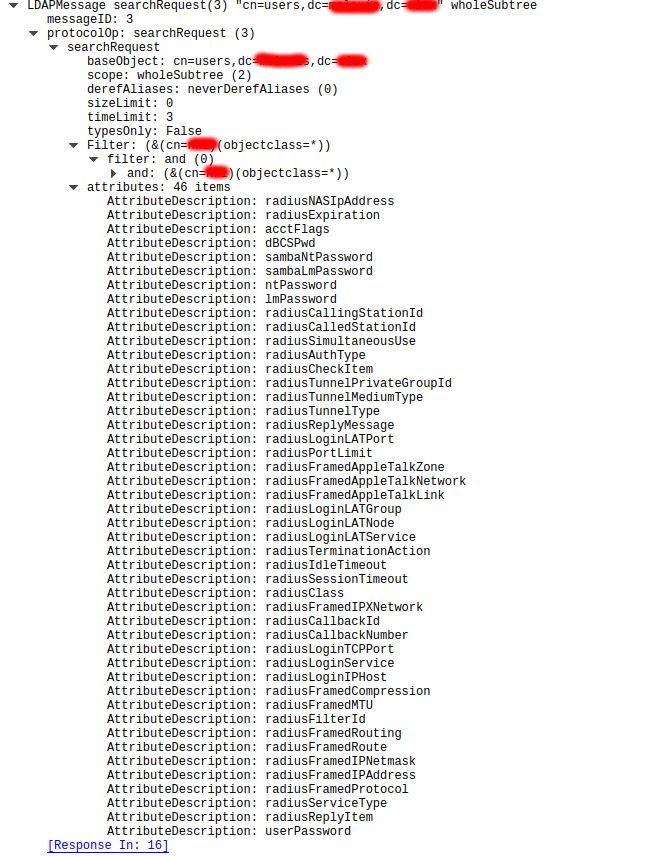
- there are attribute descriptions which are hardcoded or something which lsap search command look for:
 - in my case ldap search works correctly for the given username, however since in the cn for that particular user we have userPassword atribute, and also ntPassword and lmPassword it matches 3 entries, not only one:
- in my case ldap search works correctly for the given username, however since in the cn for that particular user we have userPassword atribute, and also ntPassword and lmPassword it matches 3 entries, not only one:
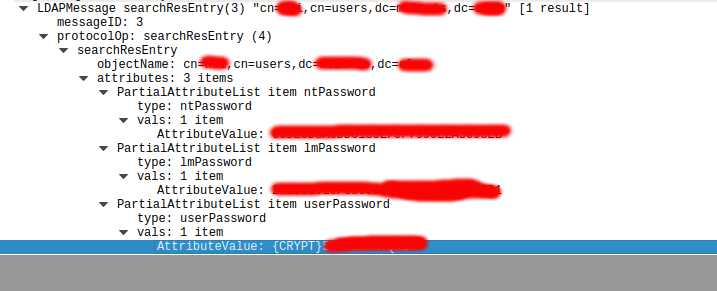 However it does not work. I tried to provide as password what is in the attribute lmPassword which is in clear text but it's not allowing me access. I think that it might be because it matches 3 fields, not only one, but I could not find where I can select which attributes to count as password. Also I am not sure if password can by in unix crypt format... Any idea?
However it does not work. I tried to provide as password what is in the attribute lmPassword which is in clear text but it's not allowing me access. I think that it might be because it matches 3 fields, not only one, but I could not find where I can select which attributes to count as password. Also I am not sure if password can by in unix crypt format... Any idea?