Hi Friend,
Policy execution method is similar in all the vendors. it is called as pyramid rule.on top of it, this rule is not to speedup the execution process rather to select the perfect one.
here is an example :
Suppose if we have to block a particular host ( Ex: 192.168.1.100) in a subnet(192.168.1.0 /24) to access TFTP, we ca write the policy in two different ways,
1. IP access list extended 199 192.168.1.0 255.255.255.0 any any permit
IP access list extended 199 host 192.168.1.100 any UDP 69 deny
2. IP access list extended 199 host 192.168.1.100 any UDP 69 deny
IP access list extended 199 192.168.1.0 255.255.255.0 any any permit
Both policies looks very similar but execution is completely different, First one will not stop the host 192.168.1.100 on accessing the TFTP because , first rule says anybody from the the subnet , 192.168.1.0 can access any thing, host 192.168.1.100 also part of the same subnet so it will be allowed, process will never check the next rule.
where as the second method is concern, we are denying the specific host therefore the host will be stopped accessing the TFTP, if any other host trying to access the TFTP, traffic will not match with the first rule so the process will execute the second rule.
bottom line is, Most specific ,means rule matching or filtering minimum hosts should come first. we should write the rules top to bottom in ascending order WRT the hosts that rule is filtering.
For your ref :
f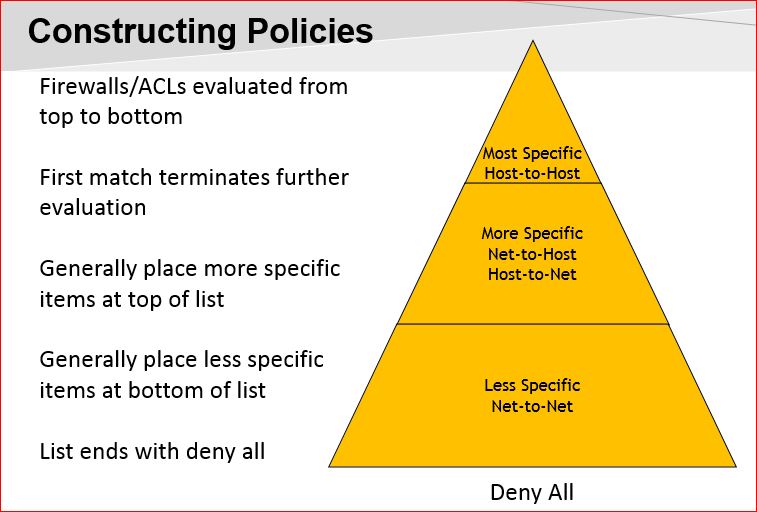
Please fee free for any further query on this.